What is OSINT and how is it used for corporate security?
Open Source Intelligence (OSINT) gives security teams the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
There are good reasons why the fictional characters like Varys (Game of Thrones) are so influential in their respective worlds. The more information you have the more you can tailor and optimise strategies for your preferred outcome. However, whereas Varys has to contend with political scheming, assassination attempts and dragons, the modern (and real) world has a much broader plethora of potential attack vectors, many of which were unimaginable just 20 years ago.
Thankfully for security professionals, the broadening net of threats exists in a symbiotic relationship with intelligence sources and security tools. What this means is that while, yes, there are now more threats to contend with, there are also more solutions and tools. For example, artificial intelligence (AI) enables Centaur approaches that far exceed human or machine only results.
In this article, we take a look at how Open Source Intelligence (OSINT) can be and is being used to arm security teams with the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
The centaur model combines machines with human insights to get optimum results.
What is OSINT?
OSINT, as the name suggests, is data gathered from all publicly (openly) available data sources. These data sources could be anything from government records or archives, online discussion forums, blogs, social media posts, or the comments on those posts.
OSINT allows you to collect data from all of those sources at once, and because of the sheer amount of information that is shared and discussed continuously on every fathomable topic, it is an incredibly powerful tool. There are billions of historical records and millions more being posted every day. You can use OSINT to identify physical threat made against your organization or executives, discover data breaches, uncover terrorist plots and even get breaking news as it is happening.
In many situations, expert data analysts with OSINT tools can identify malicious actors and discover relationships, information which can be used to enhance a privacy and security plan.
How Organizations use OSINT
The need for organizations to employ OSINT as part of their corporate security processes is becoming increasingly more evident. Interestingly though the use of OSINT has been neither formalised nor widely adopted. It often takes a particular scenario to unfold before they even consider it.
A common example is a data breach. According to the Ponemon Institute’s 2018 Cost of a Data Breach Study, the average amount of time for a company to detect a data breach was 197 days. More often than not, the organization was not the first to know either. Utilising OSINT allows you to learn of data breaches as soon as discussions begin online, for example, the hacker offers up your data for sale.
This is just one way in which OSINT is used by businesses. The use of intelligence is immensely versatile. You can detect physical threats to assets or staff, determine travel risks, discover brand hazards, secure your social media channels and cybersecurity and more.
Despite the versatility of applications for OSINT tools it still often takes a worst-case scenario for an organization to decide to finally employ OSINT solutions.
Applications of OSINT as Cyber Intelligence
Most people freely share a large amount of data about themselves. In fact, in this day and age, it’s hard not to share your data. For example, almost everyone has a phone number, this phone number is likely connected with your name, address, date of birth, and email address. It might even be linked with your broadband connection and subsequently your IP address.
As an example, in 2019 T-mobile had a significant data breach. Thankfully, it appears they spotted and responded quickly, but not before some 1 million records were exposed. They were able to mitigate the damage but not prevent it. Other companies have historically been less quick to respond such as TerraCom and YourTel America who had to pay out $3.5 million USD collectively in damages in 2015 after their data breaches. Organizations also need to remember how everyday activities expose other forms of data such as shopping habits through credit card usage and location through fitness apps.
Intelligence isn’t just important for detecting breaches or hacks. It is also vital if organizations want to protect their staff from physical threats or from being exploited via phishing scams. For example, a company’s employees will likely all have social media accounts such as a LinkedIn account which details their roles and responsibilities. This information can be paired with information from other social profiles or information shared online and can, when used properly, become valuable intelligence on how an organization runs, who’s responsible for what, and even who a malicious actor should target.
Because of the various methods that security teams can use intelligence to protect a businesses interests having a dedicated team, armed with powerful OSINT tools like Signal, could save them from serious reputational and financial damages.
Examples of threats that Signal OSINT can detect and help protect against
Counterfeit or stolen property listed online - for example, counterfeit drugs.
Employee conduct, threats and harassment on social media.
Frustrated, angry or threatening customer correspondence.
Merger, acquisition & organizational partnership discussions - this could be important for ensuring smooth operation of the supply chain, for example.
Sensitive information publicly disclosed – accidentally or intentionally.
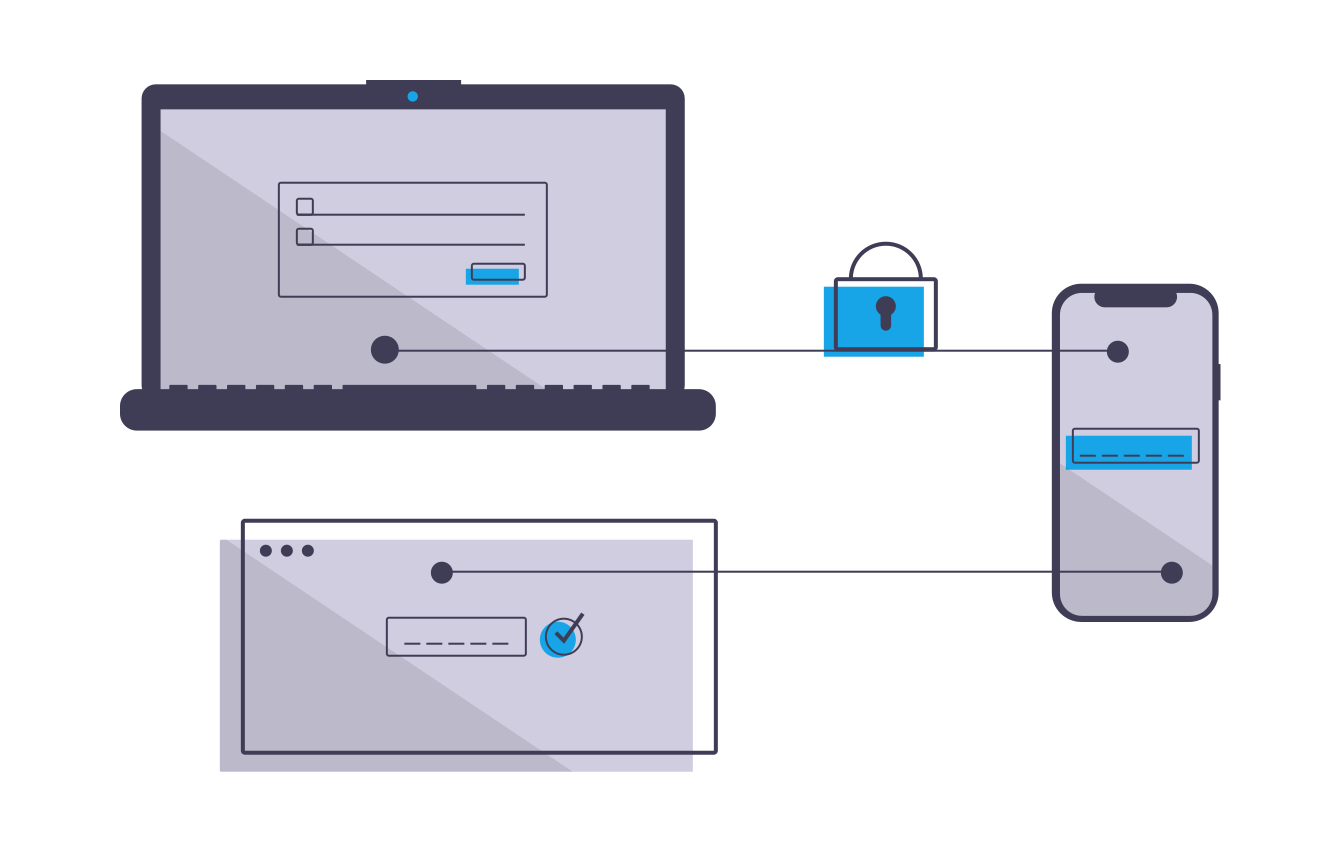
Presence of fake websites, fake invoices or scams targeting customers, staff or the organization - for example, a phishing website made to look like a banking institutes website and designed to encourage users to enter their password combination.
Credentials from data breach & compromised accounts belonging the organization.
Unsavoury relationships, membership or pending court action related to the organization.
The Results of Employing Powerful OSINT Tools
Experienced hackers and cybercriminals will understand the public nature of the channels and as such are likely to attempt to avoid actions that expose their intentions. However, OSINT doesn’t stop at the surface web, tools like Signal can give analysts and security teams access to data from sources such as the dark and deep web and even private dark web forums as well as more obscure surface websites.
The purpose of OSINT research is to provide teams with a thorough foundation of knowledge. Teams can subsequently use these insights to develop actionable plans to either prevent a threat from fully emerging, or minimise the damages of a current or recent attack.
One of the key issues that security teams and analysts face is the sheer amount of noise which might surround their brand. Invariably much of this noise is irrelevant to their purposes, however, some of it will be bad. This is why Signal assists with advanced filters applying boolean logic as well as features such as our emotional analysis tool.
How to Secure your Organization’s Social Media with OSINT Tools
We explore the risks around social media security and how organizations can utilise Open Source Intelligence (OSINT) to predict and mitigate these threats.
Social media is a powerful tool that allows organizations to reach new audiences, communicate and engage with customers, build brand loyalty, share promotions and ultimately achieve new growth. However, because of the very public nature of it, social media opens up new opportunities for cyber criminals to target an organization.
Companies which don’t take the proper precautions in securing their social media channels could find themselves reeling from unexpected attacks. These attack could implement a wide variety of threat vectors, from employees to malware, and could evolve into serious and costly threats.
In this article, we explore some of the commonly exploited risks that are associated with corporate social media use as well as what a company can do to best mitigate these risks and how Open Source Intelligence (OSINT) can play an important role in preventing and protecting an organization.
The risks of social media for corporate security
Phishing and Scams
Phishing is a predominant attack strategy by cybercriminals with an estimated 90% of incidents and breaches including a phishing element.
Phishing is defined as social engineering using digital methods for malicious purposes. Generally, the goal is to get the victim to hand over private information such as passwords, banking or credit card information.
In the case of social media, there are numerous forms that phishing can take. For example:
Impersonation
Propagating attacks
Data dumps
Romance scams
Intelligence gathering (for account takeover and spear phishing)
Social media platforms still offer only minimal controls to prevent the further propagation of account takeovers. Additionally, because social accounts typically need to be approved prior to connecting with people, account takeovers allow hackers to utilise trust associated with that account. Which is why it’s important for organizations to understand and prepare responses to these evolving threats.
Human Error
One of the key security weaknesses that many organizations face is human error. Everyone makes mistakes and in today’s digital world it is all too easy for cybercriminals to take advantage of these mistakes. In fact, according to EY Global Information Security Survey, employee weakness was responsible for 20% of all cyber attacks. Something as simple as clicking the wrong link or downloading the wrong file could cause havoc with a company's security systems.
When it comes to social media, one attack vector that many users don’t realize cybercriminals utilise is online challenges and quizzes. These quizzes often ask for or obtain by way of an answer personal information which is then used to hack passwords.
For example, the answers to a social quiz might require you to give up letters from your mother's maiden name, your date of birth, or your first pet's name. This information combined with the details publicly available on your social media profiles could very easily offer up common password and security question combinations.
Third-party Apps
Even if your company's social media accounts are locked down tight, hackers may be able to gain access to an otherwise secure social media account through vulnerabilities in connected third-party apps.
Imposter Accounts
A cyberattack doesn’t always take the form of a hack. Instead, it is fairly easy for an imposter to create a social media account that looks like it belongs to your organization. This is one reason having a verified account is so valuable.
LinkedIn’s latest transparency report notes that they took action on 21.6 million fake accounts in just six months.
Facebook estimates that about 5% of monthly active user accounts are fake.
Impostor accounts can target your customers with fake deals, disinformation, or nefarious links. When a customer is tricked like this, not only does your brand suffer but often the organization is held responsible.
One recent example found on Twitter was a fake account fraudulently collecting money on behalf of President Trump’s 2020 reelection campaign. The account “@realDonaldTrump_” is set up as an almost exact replica of the real Trump’s account with only an underscore at the end of the handle to indicate it is not the real account. And of course, it lacks that tell-tale blue verification tick.
An example of an imposter account being used to fraudulently collect money.
Unsecured Mobile Phones
More than 50% of the time spent online is done through mobile phones. Using social media apps allows us to access and engage on social channels with just a single tap. This is great, as long as you are the one in possession of your phone. However, this ease also creates a security risk.
Should your phone be stolen and accessed all it takes is one tap for the thief to access your social accounts and then they can message all your connections with phishing or malware attacks or spread disinformation using your accounts.
And, worryingly more than half of people leave their phones unlocked.
Malware and Hacks
By its very nature, social media is about social interaction. For personal accounts, this means interacting with friends or acquaintances online in some form or another. For organizations it means interacting with customers, for celebrities or influencers it means interacting with fans.
This is actually a barrier for many cybercriminals. People are generally distrustful of communications where they have no prior experience with the person or people behind them.
Generally speaking, strangers on the internet are still strangers and it takes a while to build an audience and gain their trust. For a cybercriminal to utilize social platforms then, they often have to go through a rather troublesome and lengthy process of building this trust. And while there are certainly numerous ways for a cybercriminal to sidestep these issues, if their end goal is to get people to click links or share information then their success rate will obviously be much higher should they originally share from a trusted account.
Related: The Crucial Role of Social Media Monitoring in Corporate Threat Intelligence
5 actions to securing your companies social media presence
The best policies for social media security operate around prevention. By implementing a few basic social media security protocols organizations can massively reduce the potential threats that social media might otherwise present.
Have a clear social media policy
A clear and properly implemented social media policy is the first place to start. This will allow you to not only protect against security threats but also help prevent bad PR or legal trouble that might ensue should your social media be compromised.
You social media policy should include the following things:
Outline of your brand guidelines that explain how people are allowed to talk about the company on social media.
A list of social media activities to avoid, such as the quizzes that we mentioned earlier.
Guidelines related to copyright and confidentiality
A guide on the best practices for password management to avoid threats like credential stuffing.
The expectation that employees will keep all their devices updated with the latest software.
Examples of scams and attacks and educational material on how staff can avoid these and other key security threats,
Information on who to notify and how to respond should an employee notice a security concern.
Train staff on best security practices
Building on from the previous point, because human errors are such a prevalent factor in hacks and other cyber attacks it is incredibly important to properly and routinely train staff in proper cybersecurity measures. Even the best social media policy won’t protect an organization should the staff not know how to properly follow or implement it.
Training employees routinely will also give them the opportunity to ask questions, engage and get a sense of the importance of the issue. Additionally, because cybercriminals are constantly evolving their strategies, training is an opportunity to update staff on new threats or examples of current scams.
As an added bonus, social media training also equips your team to use social tools effectively. When employees understand best practices, they feel confident using social media for their work. They’re then well-equipped to use social media for both personal and professional purposes and ultimately your company will see better results.
Limit access and permissions
One of the best ways to keep social accounts secure is to strictly control who has access and the exact permissions they have. Not everyone after all needs the ability to post, not everyone needs the ability to see the stats. And should an individual leave (especially if they leave under a dark cloud) it is important to be able to and remember to revoke their access so that they can’t use the social accounts to cause harm to the company.
Have a designated person in charge
This isn’t just a security concern, having a designated person in charge of and responsible for the running of your social channels will, first of all, ensure consistency but also ensure that someone is constantly on top of and routinely checking the social media security which will go a long way to mitigating any risks.
This person will likely be a senior person on your marketing team. They should maintain a good relationship with your company’s IT department to ensure marketing and IT work together.
Social media monitoring for threat detection
As we have mentioned several times already security threats, especially those around social media accounts are constantly evolving as cybercriminals implement new and innovative new methods for attacks. Using OSINT you can not only closely monitor not only your own social media accounts but the entirety of the web. This will allow for your security team to catch risks as they appear and neutralize potential threats early.
For example, careful monitoring of social channels will allow you to discover imposter accounts and get them shut down quickly before they can do real damage. It will allow you to spot inappropriate use of your brand by employees or others associated with your company such as a new partner.
The role of OSINT for social media monitoring and corporate security
By monitoring social networks for mentions of your brand and keywords, you’ll know right away when suspicious conversations about your brand emerge. For example, people might be sharing fake coupons or offers, or an imposter account starts tweeting in your name. Using OSINT you can monitor all the relevant activity online regarding your business and quickly identify fraud allowing you to respond to it in a timely fashion.
Additionally, you can use OSINT tools like Signal to monitor not only your social media channels for things like imposters but also for physical threats against employees or branch locations. Moreover, you could monitor for negative emotional sentiment concerning an event you're hosting and identify people who may decide to turn those threats into action.
Finally, OSINT is vital in identifying when one of the above-mentioned risks of social media becomes more than just a threat, when it becomes a reality. Being amongst the first to know when something like this happens allows you to respond quickly and effectively
Conclusion
Social media security threats are constantly changing. Hackers are always coming up with new strategies, and new scams and viruses can emerge at any time. Researchers are now anticipating that advanced attacks against social media networks will be able to leverage a user’s contacts, location, and even business activities. This information can then be used to develop targeted advertising campaigns toward specific users, or even help spark crime in the virtual or real world.
To prevent social media breaches, protect user information, and secure company data, increased vigilance by individual users and regular audits of your social media security measures are necessary to ensure organization security.
Threat Intelligence for Communications and Technology Companies
Remaining aware of the litany of evolving threats that could be and are currently being perpetrated against communications and technology companies is a priority if they want to have any hope of defending themselves against cyber or physical threats.
Communication and technology companies form an integral part of the daily activities of many individuals, companies, and governments. This sector forms a foundation of critical infrastructure which is in part what makes it such an appealing target for cybercriminals.
A successful cyberattack on a company in this sector could see vital services for hundreds of thousands if not millions disrupted. A severed internet connection could see businesses crippled and potentially shut down entire governments.
Remaining aware of the litany of evolving threats that could be and are currently being perpetrated against communications and technology companies is a priority if they want to have any hope of defending themselves against cyber or physical threats.
Telecom operators are adept at protecting their networks, additionally, with the telecom infrastructure being the primary transport for most attacks it’s also true that cybercriminals also have to rely on this infrastructure. This limits the adversaries who directly attack telecom infrastructure largely to anti-establishment hackers.
However, today, telecom organisations are recasting themselves as technology companies - which is why this article encompasses both. For instance, they are creating mobile applications for use of VoIP calls and storing data on cloud services. The lines between technology and communications companies become even more blurred with large tech companies owning parts of the infrastructure as well as those tech companies which have crossed over into the realms of communications. Apple, Facebook, and Google being the most obvious examples.
This cross-over between communications and technology creates new risk frontiers for both communication and technology companies.
“One mounting technology concern is Internet route hijacking, also known as IP hijacking, an exploit in which adversaries corrupt Internet routing tables to ‘hijack’ packets of data. Possible solutions include the implementation of secure Border Gateway Protocol (BGP), a technology that can be used globally. However, secure BGP standards haven’t been consistently adopted, and that’s not likely to happen without government incentives.”
In addition to the growing number of cyber threats, it’s also necessary to consider threats against executives as well as supply chain vulnerabilities which might be exploited. The fact that many of large organisations operate internationally, where materials and equipment manufactured in various different parts of the world is the final part of an ever-evolving ecosystem of threats.
Threats Facing Technology and Communications Companies
Today’s cybercriminals are evolving and adapting fast, discovering and creating new vulnerabilities to exploit constantly. Addressing these threats requires telecommunications and technology companies to have access to up-to-the-minute knowledge and information about threats and vulnerabilities for a vast array of potential attack vectors.
We can divide the main threats facing the communication and technologies industries into two interrelated categories:
Threats targeting companies directly.
These include DDoS attacks, targeted attacks (APT campaigns), network device vulnerabilities and human-related threats like insider access, social engineering and the risk of allowing third parties to access information.
Threats targeting subscribers of services.
Particularly the customers of cellular service providers (CSPs) and Internet service providers (ISPs). These include malware for mobile devices, subscriber data harvesting, end-user device vulnerabilities, and more.
Mobility and the Cloud
Another key issue for these industries is the proliferation of smartphones and internet-capable devices. Despite this being a pressing concern it has been found that technology and communications companies have done little to deploy security measurements with only around 45% of organisations having a mobile device security strategy in place.
As the use of mobile devices increases so does the use of cloud computing services. The cloud has been around in its modern context since at least 2006 however, it is becoming increasingly used by modern organisations with some today 50% of operators currently using some sort of cloud service.
The use of the cloud opens up new business growth avenues and increasingly optimises workflows allowing individuals to work and manage their data from anywhere on any device. However, it simultaneously creates new attack vectors which are compounded by the use of mobile devices.
Whilst organisations share increasingly more data with third parties, vendors, partners, and customers it has been found that a striking lack of security practices exists for IoT and cloud-enabled devices.
67% had an IoT security strategy.
34% had policies for secure collection, retention and destruction of new data.
36% had implemented uniform cybersecurity policies across all IoT devices and systems.
How Communications and Technology Companies are Improving Cybersecurity
Security is everybody’s business. Any member of staff might be exploited as a weakness. In a 2018 survey it was determined that 30% of security incidents were attributed to an employee compared to 23% attributed to an external hacker and 19% attributed to third party vendors. Employees could become threats in a variety of ways, accidentally or maliciously.
For example, they could be personally hacked and extorted for access to protected data. Or they could be a victim of a phishing attack unwittingly installing malware on company devices allowing hacklers to steal packages of data. Or, it could be a location or particular executive that is physically targeted for an attack. The variety of dynamic threats means that it’s not just security teams that need be involved in and informed about threats.
One trend that is true across industries including telecom and technology companies is an increased budget for cybersecurity and threat intelligence.
“It’s predicted that global spending on cybersecurity products and services will exceed $1 trillion cumulatively over the five-year period from 2017 to 2021.”
Another measure is an increasing focus on intelligence. Threat intelligence using tools like Signal allows organisations to efficiently obtain hyper-relevant data in real-time.
How is Signal being used today to protect organisations?
Company data is discovered for sale on the dark web.
Threats to an office location are found in online discussion forums.
Signal discovers an employee sharing sensitive company information online.
Final Words
Today, information security is an advanced discipline that requires the correct technology and processes paired with a skillset based on counterintelligence techniques and supported by top executives. As technology evolves new threats will inevitably appear along with a raft of new challenges.
For companies to mitigate the risks presented by an evolving threat landscape core practices such as employee security training need to be reassessed and continuously updated based on the newest information. The convergence of mobile technology, cloud services and social networking have multiplied risks - and many operators have yet to address many of these increased vulnerabilities.
These factors call for a new approach to security, one that’s driven by the knowledge of threats, assets, and adversaries. One in which security incidents are seen as a critical business risk that may not always be preventable, but can be managed to acceptable levels.