6 Ways Signal OSINT is Improving Protection for Executives and VIPs
Security teams need to be able to spot threats to executives and implement an effective response in a timely fashion. In this article, we take a look at 6 key areas that Signal OSINT is used by customers today to advance protection measures for high profile executives.
High profile executives and VIPs are more likely to receive threats of violence, be at the centre of negative online noise, and to be the target for both cyber and physical attacks. This, when paired with their busy schedules (which often involve travel), makes staying ahead of potential threats a particular challenge for their security teams.
Attackers have a variety of reasons and goals for targeting executives and VIPs. It could be anything ranging from a reaction to company layoffs, to kidnapping for ransom. Whatever the reason though, security teams need to be able to spot the threats, understand the motives, and implement an effective response in a timely fashion.
In this article, we take a look at 6 key ways Signal OSINT is used today by customers to advance protection measures for high profile executives.
How Can Signal OSINT Improve your Executive Security?
Discover private information published online
There are several reasons that an individual might publish private information online. Often, it is in anger or as some form of revenge. The kind of information that has been found published online includes: names, email addresses and logins, physical address, details about an executives families, passport details, medical information, credit card and bank details, and SSN’s.
Having such information leaks opens up an executive to a wide range of potential threats. As a security professional, it is vital to know if and when there is a data breach so that the threat can be neutralized. The longer data is available online the more risk there is. For example, if card details are discovered online the bank can be contacted and the card cancelled.
Read: Detecting and Mitigating the Risks of Data Breaches
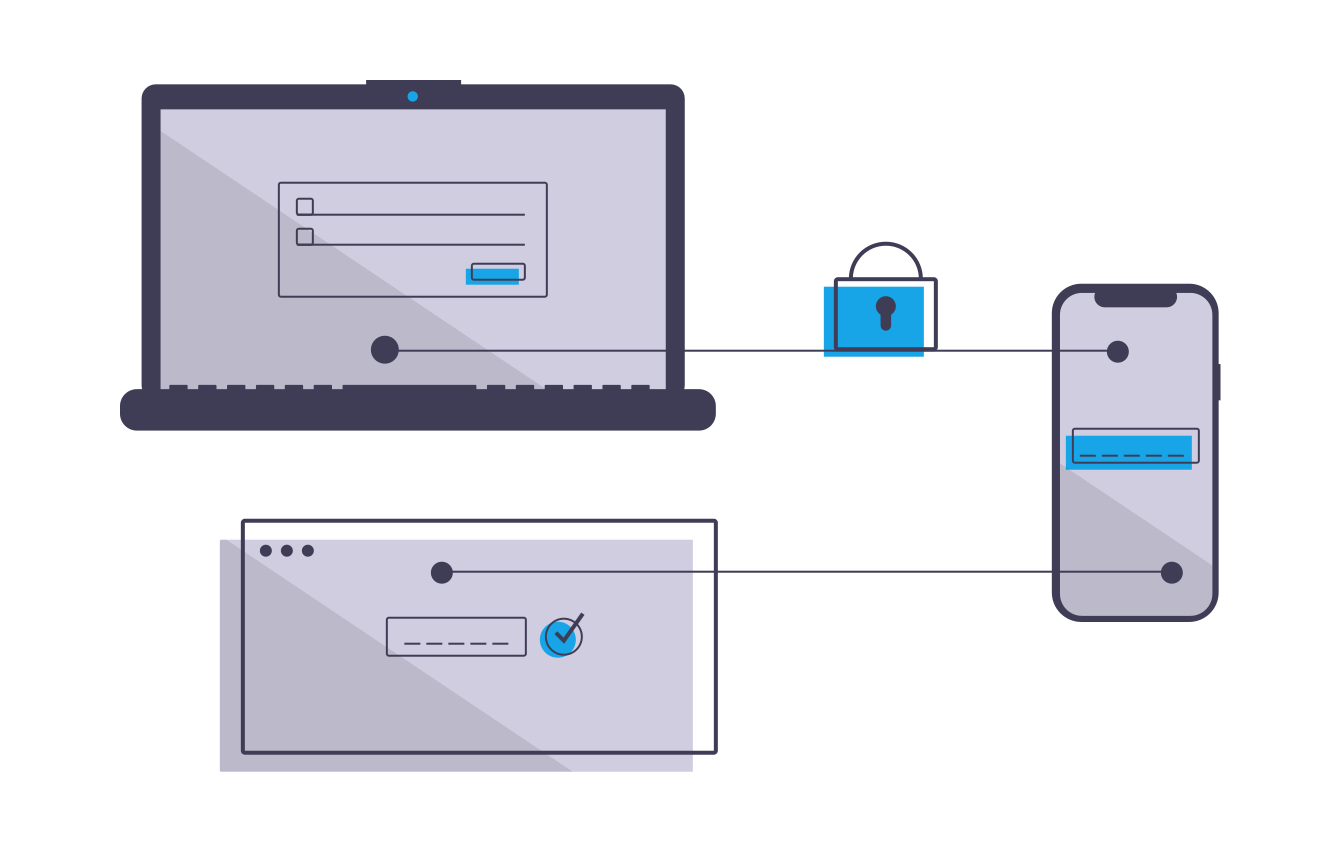
Identify direct threats
Sometimes threat actors are more direct in the way they threaten executives. This could, for example, be a direct threat of violence through an email, instant messaging service or public forum like social media. While the majority of such threats come from so-called “keyboard warriors” there are some which will require further attention and action.
For example, discussions might be uncovered on the dark web forum with details of a planned attack on an executive. With the prior knowledge of the attack action can be taken to reduce the associated risks.
One way to differentiate between someone that is simply venting their anger on a public forum and someone who genuinely might take action is to look for repetition of negative sentiment.
Emotional analysis
Emotional analysis gives data extra context which allows it to be better understood enabling a more effective and accurate response to the potential risks.
It also allows you to differentiate between when a negative comment is simply that, a negative comment, or when it needs more serious attention, for example, it’s evolving into a physical threat.
Read: When Does Negative Sentiment Become a Threat?
Misinformation is spreading about an executive
The spread of disinformation is problematic on a number of levels. For example, throughout COVID-19 misinformation has been spread regarding the virus, it’s root causes and best prevention practices. This has harmed efforts to curtail and control it. Another recent example is the role of misinformation in the 2016 US election.
There are numerous reasons that individuals and organizations spread misinformation, it could be part of a phishing campaign or an international political assault, for example. Whatever the reason the results are almost always harmful. When an individual spreads misinformation around a CEO or other executive there are real ramifications for brand and reputation which need to be managed.
To combat misinformation organizations need to be equipped with the right tools and understand both what they’re looking for, and the reasons for spreading misinformation.
Disruptive events are planned which could prove a threat to executives.
Events such as protests planned at or near an office or manufacturing location could present logistical problems and delays as well as potentially devolve into riots which would represent a physical threat. Having intelligence on the events and any salient information regarding individuals or groups looking to create trouble will allow you to take appropriate precautionary measures and prevent a threat from escalating.
Travel risks
All travel comes with some inherent risk. However, it is more pronounced for executives who are at increased risk due to the regularity of their travel and high profile.
Additionally, events like extreme weather or terrorist action may make a destination unsafe. As such, having an OSINT solution such as Signal offering an early warning of any particular dangers will enable you to plan alternative routes and otherwise avoid high risk scenarios.
Read: 4 Aspects of Effective Executive Travel Risk Management
Early warnings with real-time data
Using Signal you can create customized alerts filtered via specific keywords, phrases or even locations. We also have a built-in translation tool so that data can be searched across languages and automatically translated into your default language.
Additionally, you can run alerts through our emotional analysis tool to determine how much of a threat any particular alert is. Finally, get our optional Sapphire bolt-on and utilise our skilled data analysts to further refine your results.
This approach allows your leave your intelligence gathering on autopilot and not only effectively reduce costs but vastly increase the scope of your monitoring ability and the overall amount of hyper-relevant intelligence at your fingertips. All of this allows you to gather actionable intel in realtime.
What is OSINT and how is it used for corporate security?
Open Source Intelligence (OSINT) gives security teams the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
There are good reasons why the fictional characters like Varys (Game of Thrones) are so influential in their respective worlds. The more information you have the more you can tailor and optimise strategies for your preferred outcome. However, whereas Varys has to contend with political scheming, assassination attempts and dragons, the modern (and real) world has a much broader plethora of potential attack vectors, many of which were unimaginable just 20 years ago.
Thankfully for security professionals, the broadening net of threats exists in a symbiotic relationship with intelligence sources and security tools. What this means is that while, yes, there are now more threats to contend with, there are also more solutions and tools. For example, artificial intelligence (AI) enables Centaur approaches that far exceed human or machine only results.
In this article, we take a look at how Open Source Intelligence (OSINT) can be and is being used to arm security teams with the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
The centaur model combines machines with human insights to get optimum results.
What is OSINT?
OSINT, as the name suggests, is data gathered from all publicly (openly) available data sources. These data sources could be anything from government records or archives, online discussion forums, blogs, social media posts, or the comments on those posts.
OSINT allows you to collect data from all of those sources at once, and because of the sheer amount of information that is shared and discussed continuously on every fathomable topic, it is an incredibly powerful tool. There are billions of historical records and millions more being posted every day. You can use OSINT to identify physical threat made against your organization or executives, discover data breaches, uncover terrorist plots and even get breaking news as it is happening.
In many situations, expert data analysts with OSINT tools can identify malicious actors and discover relationships, information which can be used to enhance a privacy and security plan.
How Organizations use OSINT
The need for organizations to employ OSINT as part of their corporate security processes is becoming increasingly more evident. Interestingly though the use of OSINT has been neither formalised nor widely adopted. It often takes a particular scenario to unfold before they even consider it.
A common example is a data breach. According to the Ponemon Institute’s 2018 Cost of a Data Breach Study, the average amount of time for a company to detect a data breach was 197 days. More often than not, the organization was not the first to know either. Utilising OSINT allows you to learn of data breaches as soon as discussions begin online, for example, the hacker offers up your data for sale.
This is just one way in which OSINT is used by businesses. The use of intelligence is immensely versatile. You can detect physical threats to assets or staff, determine travel risks, discover brand hazards, secure your social media channels and cybersecurity and more.
Despite the versatility of applications for OSINT tools it still often takes a worst-case scenario for an organization to decide to finally employ OSINT solutions.
Applications of OSINT as Cyber Intelligence
Most people freely share a large amount of data about themselves. In fact, in this day and age, it’s hard not to share your data. For example, almost everyone has a phone number, this phone number is likely connected with your name, address, date of birth, and email address. It might even be linked with your broadband connection and subsequently your IP address.
As an example, in 2019 T-mobile had a significant data breach. Thankfully, it appears they spotted and responded quickly, but not before some 1 million records were exposed. They were able to mitigate the damage but not prevent it. Other companies have historically been less quick to respond such as TerraCom and YourTel America who had to pay out $3.5 million USD collectively in damages in 2015 after their data breaches. Organizations also need to remember how everyday activities expose other forms of data such as shopping habits through credit card usage and location through fitness apps.
Intelligence isn’t just important for detecting breaches or hacks. It is also vital if organizations want to protect their staff from physical threats or from being exploited via phishing scams. For example, a company’s employees will likely all have social media accounts such as a LinkedIn account which details their roles and responsibilities. This information can be paired with information from other social profiles or information shared online and can, when used properly, become valuable intelligence on how an organization runs, who’s responsible for what, and even who a malicious actor should target.
Because of the various methods that security teams can use intelligence to protect a businesses interests having a dedicated team, armed with powerful OSINT tools like Signal, could save them from serious reputational and financial damages.
Examples of threats that Signal OSINT can detect and help protect against
Counterfeit or stolen property listed online - for example, counterfeit drugs.
Employee conduct, threats and harassment on social media.
Frustrated, angry or threatening customer correspondence.
Merger, acquisition & organizational partnership discussions - this could be important for ensuring smooth operation of the supply chain, for example.
Sensitive information publicly disclosed – accidentally or intentionally.
Presence of fake websites, fake invoices or scams targeting customers, staff or the organization - for example, a phishing website made to look like a banking institutes website and designed to encourage users to enter their password combination.
Credentials from data breach & compromised accounts belonging the organization.
Unsavoury relationships, membership or pending court action related to the organization.
The Results of Employing Powerful OSINT Tools
Experienced hackers and cybercriminals will understand the public nature of the channels and as such are likely to attempt to avoid actions that expose their intentions. However, OSINT doesn’t stop at the surface web, tools like Signal can give analysts and security teams access to data from sources such as the dark and deep web and even private dark web forums as well as more obscure surface websites.
The purpose of OSINT research is to provide teams with a thorough foundation of knowledge. Teams can subsequently use these insights to develop actionable plans to either prevent a threat from fully emerging, or minimise the damages of a current or recent attack.
One of the key issues that security teams and analysts face is the sheer amount of noise which might surround their brand. Invariably much of this noise is irrelevant to their purposes, however, some of it will be bad. This is why Signal assists with advanced filters applying boolean logic as well as features such as our emotional analysis tool.