5 Lessons Organizations Can Learn from the Worst Data Breaches of 2020
In this article, we take a look at 5 of the lessons that can be learnt from some of the biggest cyberattacks of 2020.
While data breaches are invariably costly for organizations, the fallout from a data breach isn’t always the same. There are numerous motivations for threat actors and an even greater number of strategies that they employ to achieve their varied goals. As such, it falls to security professionals can continuously learn from the ongoing cyberattacks the best ways to predict and prevent cyber breaches in a constantly evolving threat landscape.
In this article, we take a look at 5 of the lessons that can be learnt from some of the biggest cyberattacks of 2020.
1. 3rd party integrations create new attack surfaces
The recent breach of SolarWinds allowed foreign agents to access and spread malware to numerous government agencies and high-value US targets. These threat actors knew they could likely never penetrate these targets directly, and instead discovered they all used the same software for network management - SolarWinds.
The attack spread a malware which lay unnoticed in the system for months as the attackers are believed to have observed and gathered data on their targets.
The key take away from this hack is that no matter how excellent and strict your own system’s security is, if the 3rd party systems you use have a weakness, then so do you. This is especially important as systems become increasingly interconnected, with a myriad of moving parts provided by dozens of different vendors.
While you can’t and shouldn’t simply wall of your systems with a trust no-one approach, organizations also mustn’t take third-party solution provider’s security for granted. Conduct rigorous, ongoing security audits of your systems to be sure there’s not a nasty surprise hiding around the corner.
2. You need clarity across your organization’s security
As an organization grows in size and complexity, often, as we mentioned above, integrating and employing 3rd party vendors, the number of attack surfaces grows too. Organizations need systems in place to maintain clarity over the entirety of their IT security.
In July, Garmin was locked out of its own systems by ransomware and ended up having to pay millions in ransom for the decryption key.
Garmin faced an impossible situation. While law enforcement officials and cybersecurity experts repeatedly warn companies not to pay ransomware attackers as it encourages further ransomware attacks, companies like Garmin are often left with no other choice.
As such, companies need to employ systems, security protocols, and training to prevent ransomware.
For businesses like this, it’s vital to have systems in place to maintain a vigilant security posture toward every possible vector for attack.
3. Humans are the weakest link
Social engineering tactics can range from rather obvious emails from Nigerian princes to complex multi-step and highly targeted spear-phishing campaigns. In late 2020 the latter is what happened to Twitter, with numerous employees targeted with a strikingly elaborate spear-phishing campaign. The strategy involved multiple steps including tricking an employees phone carrier, pretending to be a member of the I.T. team, and creating fake login pages.
Once they had an employees admin account login they hijacked multiple high profile Twitter accounts and launched a Bitcoin scam that saw them making off with over $100,000 in less than an hour before it was stopped. Though this attack certainly could have been worse, it shows how one of a companies biggest vulnerabilities is compromised employee credentials.
There are a couple of things that can be done to protect against employee weakness in your security defences. These include restricting employee access to sensitive data. Ensuring you offboard, and remove access to systems for old employees, implementing strong authentication protocols such as multi-factor authentication, and regular security training sessions for staff
4. Only store data vital to providing your service
In July of 2020 GEDMatch, a DNA genealogy site was hacked. The hackers changed the user’s privacy settings - opting everyone in to share their data with law enforcement. The hack exposed the data of around 1.4 million people.
Thankfully, GEDMatch later announced that no raw DNA files had been compromised as no raw data is stored on the site. Instead, the data is encoded when it’s uploaded and the raw file deleted immediately. The key lesson here is that GEDMatch followed good practice, not storing any sensitive raw data and thus eliminating a potentially serious attack vector meaning the failure of one control did not lead to the attackers progressing beyond their initial intrusion.
If you can avoid storing highly sensitive data — such as passwords, payment information, or biometric data — on your own servers, do so. Deleting raw DNA data helped minimize the damage to GEDMatch in this breach.
5. People aren’t going to stop reusing passwords
The majority of people on the internet don’t know the best online security practices and many reuse the same tired old password across numerous websites. This has lead to a rise in popularity of one of the most common attack strategies employed by threat actors, credential stuffing. This is when they buy large datasets of login details, eg. passwords and user names, and apply them to other sites. While the strike rate is generally quite low, this strategy of credential stuffing does work. This is what happened to several insurance companies in 2020 including Independence Blue Cross.
Independence Blue Cross reported that their member portals had been improperly accessed by hackers reusing credentials stolen from MyFitnessPal in an attack from 2018.
People aren’t going to stop reusing passwords anytime soon, but businesses can still guard against credential stuffing. One crucial step is to implement strong authentication protocols such as multi-factor authentication or adaptive authentication, which asks users for more credentials if their behavior is suspicious. In this case, it could have noticed that members were logging in with new I.P. addresses or at an unusual time of day, and asked them to confirm their identity.
Final Words
Organizations are increasingly connected online, using a myriad of integrations and tools to create better, more user-friendly solutions. Additionally, as we all become more technologically literate and engage more and more online there is an increasing amount of users data stored on organizational systems.
This means that the number of attack surfaces that organizations have to be aware of is continuously growing, and so too are the opportunities for attackers to achieve their goals. Whether it’s foreign espionage, idealogical fanatacism, or for personal financial gain.
Ultimately, we’re all in this together, a data breach or successful attack on one company could easily have ramifications against your own organizations. As such, employing the right tools, such as an OSINT tool like Signal, to monitor, detect and better protect against potential threats in this growing threat landscape has never been more important.
How can 4chan be Used as a Data Source for Security Intelligence?
4chan is just one of the data sources you can monitor using Signal. You can find conversations by alt-right groups, threats of violence against a person, organization or group, and more, which makes it a valuable data source for security professionals.
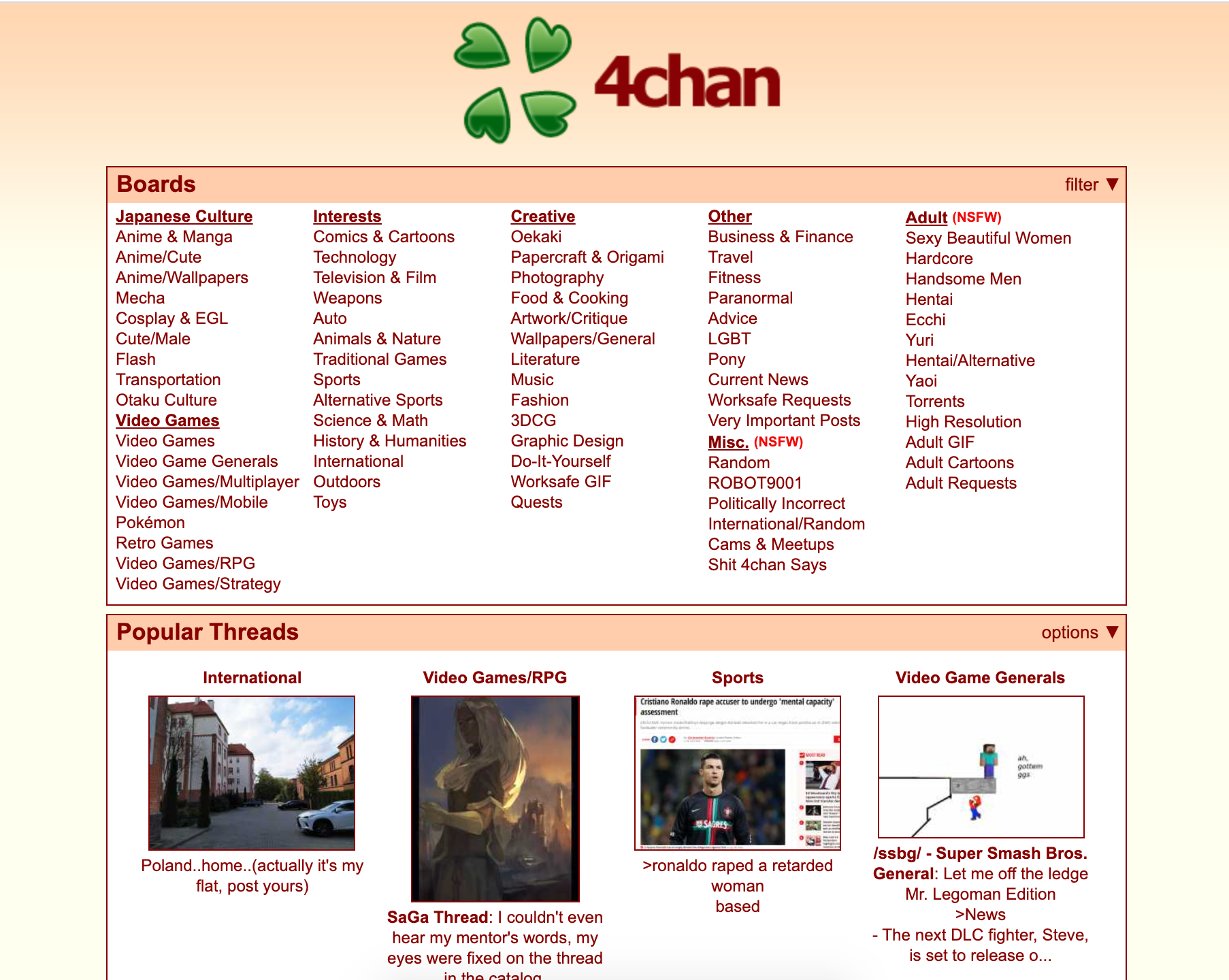
What is 4chan?
4chan is one of the largest English language based image boards on the open web. They have over 900k new posts per day and some 27 million active monthly users.
What makes it a unique social platform is that users can choose to remain anonymous. They don’t even need to create an account to access and engage with content on the platform. As an added security measures, posts time-out after a period so they can’t, unless found and archived by an independent data gathering source, be checked and referenced by security teams, users, or law enforcement at later date.
There is a wide range of topics hosted on the platform, from Japanese culture, to politics, to adult content. Because of the anonymity allowed, as well as a very limited moderation by the site owners, 4chan has a large amount of illicit content and activity. This activity includes cyberbullying, child pornography, harassment, violent threats, racism and extremist ideologies.
Despite this, it’s important to note that there is nothing inherently bad about the platform, just as there is nothing inherently bad about the dark web, and many of the users use it for legitimate purposes such as for its original intent which is the exploration and discussion of the Japanese film and television animation style, anime. In fact, like Reddit, many influential memes have originated from the platform such as ‘lolcats’ and ‘chocolate rain’. As such it has historically been an important driving force behind the development of internet culture.
Bottom line: 4chan is a forum, the original purpose was for the discussion of anime and Japanese culture. It’s a forum where users don’t need to have an account or sign up with a name, there is little moderation, and posts are deleted from the server after a period, as such there are few consequences. With this format, people can and do say just about anything on the platform.
How can 4chan benefit your organization as a data source?
The anonymity offered by the channel means users feel comfortable talking openly and they do so around a wide range of subject matters and people. For example, under the political forum /pol/ you can find examples of alt-right groups, threats of violence against a person, organization or group, and racist behaviour.
The range of topics discussed and the freedom with which individuals and groups openly discuss them can give security teams and law enforcement an idea of emerging trends as well as be one of the first places that death threats or threats of violence against individuals and organizations can be found. In the past, terrorist manifestos have also been posted on the channel. These discussions can indicate when an event is going to evolve into a tangible threat and give security teams a heads up to prepare and mitigate the potential threat.
Additionally, there are groups and individuals on the channel, such as the members of Anonymous who have turned their online attention, for right or wrong, to intelligence gathering on people and organizations. Often, 4chan is one of the first places they share their findings. For example, they might uncover and share personal details about a CEO such as their address, medical records and details of their family.
Why use Signal for monitoring 4chan?
One of the key problems with any form of online intelligence reconnaissance is the quantities of data you need to assess to get even the smallest tidbits of potentially useful information. 4chan has this problem in spades with over 3.5 billion posts. And these posts are transient, with the more R rated the post being the shorter it’s existence. This means relevant security intelligence on the 4chan platform might only be public for a couple of days. To gain real insights into the channel you need to be constantly and efficiently monitoring with real-time alerts.
4chan is just one of the data sources you can monitor using Signal though. You can simultaneously monitor the open, deep, and dark web including forums like Reddit and chatrooms like Telegram. Our system allows you to create tailored keyword-driven searches with boolean logic which is assisted by our machine learning and language processing AI to efficiently gain intel on hyper-relevant, new and emerging threats.
The Increasing Risks and Rising Costs of Data Breaches
The average cost of a data breach is estimated to be over $3million USD and rising. As such it’s never been more important for organizations to have the tools and processes to mitigate the threat of a data breach.
Data Breaches Aren’t Uncommon
It’s not just small companies with limited security budgets that have exploitable cyber gaps. Often, in fact, large organizations become targets because of the amount and nature of the data that they hold. Organizations in the healthcare sector, for example, have proven time and again to be a popular targets for cybercriminals.
Another example of a large organization being targeted is Experian. Experian experienced a major data breach in August 2020 where over 24 million records were exposed. The attackers impersonated a client and were able to request and obtain confidential data. Experian claimed that no customer banking information was exposed. Even so, personal information like this could be used in a targeted social engineering strategy to then get Experian customers to reveal further sensitive information such as their banking details.
This isn’t the first major data breach that Experian has had. Back in 2015, 15 million North American customers and applicants had their personal data, including Social Security numbers and ID details, stolen. Perhaps because of this prior experience, Experian understands the risks and are adept at dealing with cyber breaches. They claim that the attacker’s hardware has already been seized and the collected data secured and deleted.
How Much Does the Average Data Breach Cost?
The answer to this question varies between country and is additionally dependent on the sector but in general, can span anywhere from $1.25 million to $8.19 million.
According to the 2020 report from IBM and the Ponemon Institute the average cost of a data breach in 2020 is down 1.5% since 2019 and cost around $3.58 million USD. This works out to be around $150 per record and is a 10% rise over the last 5 years. The report analyzes recent breaches at more than 500 organizations to spot trends and developments in security risks and best practices.
The cost estimate includes a combination of direct and indirect costs related to time and effort in dealing with a breach, lost opportunities such as customer churn as a result of bad publicity, and regulatory fines. Though the average cost of a breach is relatively unchanged, IBM says the costs are getting smaller for prepared companies and much larger for those that don’t take any precautions.
Interestingly, various industries including healthcare appear to be more susceptible targets for attackers. According to the report, healthcare breaches cost organizations $6.45 million per breach, a number that eclipses all other sectors and makes it the ninth year in a row that healthcare organizations have had the highest costs associated with a data breach.
The average cost for per breached healthcare record ($429) is more than double any other industry too and substantially higher than the average, $150, according to the report. Healthcare breaches can often take the longest to identify (up to 236 days) as well.
Data Breaches are Happening all the Time
Data breaches are occurring constantly. Records from large brands with big security budgets and teams as well as much smaller organizations. It’s important that everyone understand the importance of secure digital practices and explores strategies for educating staff to reduce the risk of social engineering tactics.
How do Data Breaches Occur?
Hackers use various strategies to gain access to data. For example, with Experian the attacker leveraged human weakness through social engineering to persuade an employee to give them the data. Other strategies could be exploiting weaknesses such as a misconfigured or unsecured cloud storage. Alternatively a data breach could be the result of a malicious malware or ransomware.
According to the IBM/Ponemon report around 40% of all incidents were actually due to either cloud misconfigurations or stolen login details. Because of this IBM has urged companies to reexamine their authentication protocol to ensure 2FA is active.
A final note on the ascertaining of data by attackers is around state-sponsored attacks. State-sponsored attacks only make up around 13% of the overall number of attacks according to the report. However, with an average associated cost of around $4.43 million it’s clear that these types of attacks tend to target high-value data and this results in a more extensive compromise of victims' environments.
The energy sector, commonly targeted by nation-states, saw a 14% increase in breach costs when compared to the prior-year period, with an average breach cost of $6.39 million.
How can Organisations Reduce the Cost of Data Breaches?
“The average time to identify and contain a data breach, or the "breach lifecycle," was 280 days in 2020. Speed of containment can significantly impact breach costs, which can linger for years after the incident.” - Source
By having mitigation measures in place IBM/Ponemon estimate companies can reduce the cost of a breach by an average of $720,000.
According to their report those companies which had automated technologies deployed experienced around half the cost of a breach ($2.65 million on average) compared to those that did not have these technologies deployed ($5.16 million average).
Security response times were also reported to be ‘significantly shorter’ for companies with fully deployed security automation – these companies are as much as 27% faster than their counterparts at responding to breaches.
Security tools like OSINT platforms not only enable a faster breach response but a significantly more cost-efficient one as well, which as the security professional shortage persists is of absolute importance.
Signal OSINT platform gives you hyper-relevant real time alerts from surface, deep, and dark web sources.
Final Thoughts
With our increasing levels of digitisation, our growing reliance on the cloud, and the complexity of security systems paired with human error there are more attack vectors than ever before for hackers to exploit.
A data breach could involve anything from publicly available data being scraped and sold off to spammers, to online banking and credit card information being stolen. The longer a data breach goes undetected the longer the threat actors have to utilize this data causing more harm as time goes on.
Having the right tools and processes in place will allow you to detect data breaches early or even prevent a data breach from happening in the first place. With the steadily rising cost associated with data breaches, this could save an organization millions in the long run.