Leveraging Telegram as a Data Source for Open Source Intelligence
Conversations on public Telegram groups can offer valuable insights into ongoing and potential criminal activity making it a valuable data source for security professionals.
People are increasingly aware of how their data is accessed and used, whether this is the security of their private conversations, their online browsing history, or even Personal Identifiable Information (PII). With this increase in consciousness for data privacy, chat applications have had to promise better encryption and anonymity if they are to compete.
As such, over the last few years new chat apps, with a primary USP of better privacy have hit the market. This includes the likes of Telegram and Discord. The anonymity and data security offered by these apps have quickly made them popular with both legitimate users and criminals. On Telegram, you don’t have to look too hard to uncover conversations around the sale of illicit goods, examples of extremist views and hate speech, the trading of PII, and more. It’s also worth noting that many marketplaces and forums on the dark web also have chat groups on Telegram.
Many of the groups and channels on apps like Telegram are open to the public, allowing users to easily reach a large potential market relatively risk-free. Not all groups though are open to the public making it substantially harder for security professionals and law enforcement to monitor these channels successfully.
However, with a tool like Signal, you can view and monitor data from many of these closed communities and hard to access groups easily and efficiently.
About Telegram
Telegram is a messaging app that was launched in 2013. It focuses on supplying a fast, free and above all, secure messaging service. The chat app has end-to-end encryption and several other features which add to it’s perceived security. These features include “secret chats” which store data locally, a timer on messages to self-destruct after a specified time, notifications of screenshots, and messages in secret chats can’t be forwarded. Their main USP is to provide a service where data is protected from thirds parties, including any curious government or security agencies.
Unlike other chat apps, Telegram promotes itself as providing its users with full anonymity, including the ability to set up a unique username and make your phone number to private. It’s because of these security features as well as the offered anonymity that the application quickly became a popular choice for criminal communications.
How Can You Leverage Data from Telegram for OSINT?
There are various channels and groups on the Telegram app in which illicit and criminal activity is discussed or undertaken. This ranges from the sale of illegal goods, stolen data, to planning physical attacks on an organization or individual.
For example, on the group “Carders” on Telegram, a group which has over 5,000 members you can find stolen credit card details including full numbers and CVV codes. This chat group is linked to an online shop getbette.biz (which was taken down in early 2020). Most of the conversations in this group revolve around some form of financial fraud, whether that’s leaked card details or the sale of PII.
On other Telegram groups, you can find details for hacked personal accounts like Netflix, Disney Plus, Amazon Prime etc. These logins might be sold for a variety of reasons, such as credential stuffing, or for personal use.
It’s not just dealing in illegally obtained data though. Telegram is used for a broad variety of purposes. A particularly popular one is the sale of drugs. Narcotic Express DE is one such group. With close to 1,000 members, this German group is a closed group which focuses on the purchasing, sale and distribution of drugs.
Closed groups cannot be found in a search within the app or in the dedicated Telegram search engine, instead, you have to be invited and sent a link by another user in the group. In addition, users can only see posts, not post themselves into the group.
Other examples of leveraging Telegram as a data source include monitoring for:
Hate speech and death threats,
Hacking services for sale,
Exploit kits,
Data breaches,
Hate groups.
Using Telegram as an OSINT Source
As outlined above, are plenty of conversations of interest that happen through the Telegram app and its various groups. These groups can offer insight into criminal activity and better enable organizations to protect their assets and staff from emerging threats. For example, you might find information on a recent data breach through the app. Having this early knowledge of the breach is essential for mitigating costs.
However, as with any potential data source, it’s not a case of simply downloading the app. Efficiently scanning and monitoring the platform for potentially relevant or information of interest requires the right tools.
First, groups like Narcotic Express DE are closed groups, meaning locating and gaining access to them is a challenge in itself. Secondly, with features such as message self-destruct constant surveillance is necessary. These challenges mean time and resource need to be devoted to this specific channel, time and resource that might be better spent elsewhere.
Using an OSINT tool gives users the ability to access and utilize hard to reach data sources like Telegram. Data from Telegram is gathered by our data provider Webhose, who scrape the publicly available data from both open and harder to access closed groups continuously. Signal users can set up searches with Boolean logic, selecting Telegram as one of the data source options available.
12 of the Biggest Ransomware Attacks of 2020
Ransomware can cost an organization millions and often the victim has no alternative but to pay. In this article, we look at 12 of the biggest ransomware attacks that occurred in 2020.
Ransomware is a form of malware which is installed on a victims device or devices with the main objective of seizing and/or locking away sensitive data. As the name suggests in order for a victim to regain access to their data and systems they need to pay a ransom. More often than not, the two options a victim is presented with when they succumb to a ransomware attack is to either rebuild their systems from scratch and potentially have the attacker leak the data online - or pay up.
As such, it’s unsurprising that, in our increasingly digital age with more and more data on the cloud, that the number of attacks and the success of ransomware attacks is on the rise. Approximately 58% of ransomware victims paid in 2020, compared to 39% in 2017.
Ransoms for these kinds of attacks range from a few hundred dollars to thousands or even millions of dollars payable in cryptocurrency such as Bitcoin. In return for the payout, the attackers will release a decryption key allowing the organization to return to business. Certain industries, such as government organizations and hospitals are more susceptible to ransomware attacks due to the nature of the work that they do often being time-sensitive. For example, a ransomware attack crippled a hospital in Germany, leading directly to one patient’s death.
There are numerous strategies that ransomware attackers employ to gain access to a victims database. One of the most common though is through social engineering tactics, such as phishing emails. Cybercriminals can make these emails look exactly like trustworthy emails from official sources, tricking victims into downloading compromised software onto their device.
Because of the nature of social engineering tactics, and the evolving cyber threat landscape no organization can ever be fully secure from malware threats. Below we outline 12 of the biggest ransomware attacks that occurred in 2020.
12 Ransomware Attacks that Happened in 2020
1. ISS World
Estimated cost: $74 million
In February of 2020 ISS world, a Denmark based company went down due to a ransomware attack. Thousands of employees were left without access to their systems and emails. This cost them an estimated $74 million which includes regaining control of the affected IT systems and re-launching critical business systems.
2. Cognizant
Estimated cost: $50 million
A ransomware attack on the organization Cognizant in April of 2020 is said to have cost the company over $50 million, potentially as much as $70 million, including legal and consultation costs and data recovery costs, along with the financial loss reflected in their second-quarter earning in 2020.
3. Sopra Steria
Estimated cost: $50 million
The company Sopra Steria revealed that they were hit by hackers using a new version of the Ryuk ransomware in October.
They estimate that the fallout, including dealing with the various systems that went out of action, is likely to have a gross negative impact on operating margin of between €40 million and €50 million.
4. Redcar and Cleveland Council
Estimated cost: $14 million
Redcar and Cleveland Council in the UK suffered an attack on their systems in February of 2020 costing the council an estimated $14 million. The ransomware attack is said to have disrupted the company’s network, tablets, computers, and mobile devices for 3 full weeks. The council announced that in March, that it could take months for a full recovery and estimated the overall costs to be between $14 - $21 million.
5. Software AG
Estimated cost: $20 million
Software AG is the second-largest software vendor in Germany. They were reportedly hit with the Clop ransomware in an attack in October of 2020. The company disclosed that the ransomware attack disrupted a part of its internal network but didn’t affect customer services. The cybercriminal group responsible demanded a $23 million ransom.
7. Travelex
Estimated cost: $2.3 million
It was reported that Travelex the money exchange firm was hit with a file-encrypting malware attack which shut down its internal networks, website and apps for several weeks. Reportedly Travelex paid a ransom of $2.3 million in BTC to the dark actors to regain access to their data and restore services.
8. University of California San Francisco (UCSF)
Estimated cost: $1.14 million
UCSF was targeted by a malware attack which encrypted servers used by the school of medicine impacting students in June of 2020. The ransomware was prevented from travelling to the core UCSF network and causing more damage. The authorities negotiated with the cybercriminals and UCSF ended up paying approximately $1.14 million in ransom of the $3 million demanded.
9. Shirbit Insurance
Estimated cost: $1million
After a cyberattack on the Israeli Insurance provider Shirbit in December of 2020 the attackers demanded roughly $1 million in Bitcoin. In order to pressure the company into paying they demanded immediate payment or an increase in the ransom cost, doubling after 24 hours. Additionally, to show they weren’t empty threats they dumped the first 300 records online, again threatening to dump additional records every 24 hours until they received payment.
10. Communications and Power industries
Estimated cost: $500,000
California-based Communications & Power Industries (CPI) makes components for military devices and equipment, like radar, missile seekers and electronic warfare technology. The company counts the U.S. Department of Defense and its advanced research unit DARPA as customers. Reportedly, CPI paid $500,000 to obtain the decryption key to unlock their servers and return services.
11. Grubman Shire Meiselas & Sacks
Estimated cost: $365,000
Grubman Shire Meiselas & Sacks is a law firm that specializes in law for those in the media and entertainment industry. Their clients consist of a range of A-list celebrities and, with such high profile individuals on the line, the stakes for them were extremely high. They were targeted and files encrypted by REvil ransomware. The firm agreed to pay an estimated $365,000, however, the attackers started demanding more afterwards and the company has since kept quiet on what it has or is willing to pay.
12. Tillamook County
Estimated cost: $300,000
Tillamook county in the US was attacked by cyber attackers in January. The attack interrupted their email network, phone systems and website. After exhausting alternative options, they estimated the costs to restore service would cost well over $1 million and take several years and opted instead to pay the $300,000 ransom.
Keeping your data and organization secure
Never click on suspicious links or any links attached in unsolicited emails.
Back up systems and data continuously. Create a separate data-backup in an external hard drive that is not connected to your computer, so that you don’t have to pay the ransom if a ransomware attack happens.
Never disclose personal information over the phone or over email.
Educate employees of cybersecurity best practices and social engineering tactics that may be used against them.
Limit employee access to sensitive data to reduce attack surfaces.
OSINT Tools and Mitigating Costly Ransomware Attacks
Early warning of data beaches through OSINT tools can help you predict and prevent cyber attacks as well as enable organizations to take mitigating actions faster. While open-source intelligence tools can’t prevent ransomware, they can help organizations reduce the risks and potential damages.
OSINT tools can be used by organizations to monitor their supply chains, allowing them to learn of potential disruptions in real-time and enabling them to implement contingency plans fast.
Additionally, organizations can use tools like Signal to monitor for ransomware and malware currently being used. This can help security teams determine emerging threats being used against other organizations in their industry to better inform ongoing cybersecurity best practices.
Ultimately, by using OSINT to monitor darknet forums and market places security professionals are able to learn about the newest strategies being employed, the most recent weaknesses being exploited, and the most current software being utilized. Armed with this knowledge they are much more able to develop effective countermeasures as well as actively prevent ransomware infection.
Stopping Organized Retail Crime with Improved Situational Awareness
Organized retail crime is the substantial theft or defrauding of a retailer by an organized group of people as part of a larger criminal operation.
What is Organized Retail Crime (ORC)?
Organized crime continues to be a growing concern for the retail industry. 97% of those surveyed said they've been victimized by ORC in the past 12 months. When we talk about ORC, we aren’t talking about a few teenagers slipping sunglasses into their bags. We are talking about the substantial theft or defrauding of a retailer by an organized group of people as part of a larger criminal operation.
The primary objective of these criminals is to turn a profit. This means their theft is rarely, if ever for their own personal use. Instead, they employ strategies such as obtaining illegitimate refunds for stolen goods, thefts of credit card information from vendors, or reselling those aforementioned stolen goods.
Typically for these organizations to operate profitably they need to steal in substantial quantities. In fact, it is estimated that retailers had an average loss of $703,320 per $1 billion in sales directly due to ORC in 2019. The scale of the organized retail crime operations can be devastating for retailers and are responsible for billions of dollars worth of losses each year in the retail sector.
Many factors play into this, including rising felony thresholds that reduce the risk for ORC criminals. In addition, respondents say ORC gangs are becoming more violent. And over 2/3rds of those questioned said they’d seen an increase in ORC activity.
Types of Organized Retail Crime
There are two main ways that retailers are targeted. This is either through retail fraud, where the threat actors implement one of many fraudulent strategies to make a profit at the harm of the retailer. Or they steal product from the retailer and resell it usually through e-commerce channels or even dark web commerce sites.
Fraud and Organized Retail Crime
Refund or Return Fraud - This is when an individual or group returns merchandise they stole for cash or credit from the store. An alternative strategy involves attempting to return counterfeit merchandise.
Counterfeit Money - Groups use counterfeit money to make numerous purchases from across a range of stores to avoid suspicion. Then they return the products for real cash or they sell the product online. Alternatively, they might purchase gift cards and then sell those on for real cash.
Serial Number Fraud - The organization might legitimately purchase goods and then sell the serial number for a replacement claiming it has broken. Often, replacement goods are sent before the damaged ones are received by the retailer. They can then make a profit off of the fraudulently claimed item.
Gift Card Fraud - There are a few ways that gift cards can be used by organized retail crime groups. First, a stolen credit card could be used to buy gift cards. Second, gift cards often have fairly simple serial number sequencing, attackers can learn the sequence of the cards and when they are legitimately loaded, make a clone of the card to sell or use themselves.
Credit Card Fraud - Because of the amount of transactional data that retailers have they are a prime target for hackers. These hackers could be looking for credit card data, banking details, or simply, personal information data. This they will likely sell off to the highest bidder through a dark web marketplace rather than use themselves.
Theft and Organized Retail Crime
Mass Shoplifting - This can take various forms. One, a group goes around separately to various different retailers and boost a substantial amount of merchandise without anyone noticing. Alternatively they might take a smash and grab approach, where a large group rush into a store, grab what they can, and rush out just as quickly. Potentially making off with thousands worth of goods.
Robbery - This is when an individual or group targets a specific retailer, often for cash in the till. This kind of robbery can be violent and safety should always be the primary concern for the retailer.
Smash & Grab / Burglary - Organized retail crime groups have been known to target high-quality retail stores for high-value merchandise they know they can profit from. For example, designer clothing, electronics, and jewellery. This could involve smashing the front window with a brick or a more subtle entry involving access through air vents or by manipulating an employee to gain access after closing.
Cargo Theft - One of the key strategies employed by organized crime groups is the theft of cargo. Cargo is defined as merchandise that has yet to reach its final destination. Examples of this include theft from warehouses or from lorries whilst they are in transit. This allows for the criminals to steal large quantities of goods in one go.
73% of retailers surveyed said they've been a victim of cargo theft in the past year. En route from distribution center to store is the most commonplace for cargo theft to occur.
Improved Situational Awareness for Preventing and Mitigating Threats Associated with ORC
To combat the threat of organized retail crime, 65% of retail executives surveyed said they were prioritizing ORC more now than 5 years ago. To do this 56% said they have or plan to allocate additional technology resources to fight risk and 44% said they would be increasing their loss prevention budgets (source).
Loss prevention strategies include more stringent return policies, better gift card serializing, electronic article surveillance, and improved video surveillance. To improve the overall effectiveness it’s also important to support loss prevention teams with accurate and up-to-date intelligence.
Using OSINT tools like Signal you can quickly become aware of and mitigate damages from a range of potential threats from organized retail crime such as:
Cloned gift cards for sale on the dark web.
A conversation suggesting cargo was going to be targeted.
Data breaches of sensitive customer data.
Plans for after hours break-ins.
Product serial numbers found for sale on Telegram.
Stolen goods found online.
5 Dark Web Marketplaces Security Professionals Need to Know About
We take a look at how security professionals can overcome the plethora of challenges that come with finding, accessing, and efficiently monitoring dark web marketplaces for information security.
Dark web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. The goods and services on offer range from leaked credit card details, exploit kits and hackers for hire, to advertisements for hitmen services.
Because of the range of goods and services found for sale, as well as the conversations that occur around these sales, dark web marketplaces can be immensely valuable sources of data on criminal activity. As such, they are normally under intense scrutiny from law enforcement and security professionals alike.
5 Dark Web Marketplaces
People have been organizing illicit trades via the internet since the 1970s. Those early examples though were through closed networks and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail, but easy. As such, the trading of illegal goods online has become more commonplace and vast dark web marketplaces have been created.
The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. Silk Road was created by Ross Ulbricht in February 2011. Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013, and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services.
ToRReZ
ToRReZ Market is a wallet-less market; which means you only send funds when making an order. The market currently supports four cryptocurrencies: Bitcoin, Monero, Litecoin, and Zcash. Both physical goods such as drugs, and digital goods such as software and credit cards, are sold on ToRReZ Market.
Tor2door
Tor2door is a darknet marketplace that launched in June 2020. The market is built from scratch and has a unique design. Tor2door claims that security and usability are its main priorities. This market is one of the easiest to use and is very simple for inexperienced dark-net users.
Hydra
Hydra is the largest marketplace in the darknet and most popular darknet marketplace in the Russian-speaking sphere. According to the Project news outlet, it is responsible for 64.7 billion rubles ($1 billion) in sales through its 5,000 shops between 2016 and 2019. Although a wide range of illicit goods and services are sold, the site also has a few rules, which are perhaps one of the reasons for its longevity and success. These rules include no fentanyl, no weapons, no sale of hitmen services, viruses, or porn.
Versus Project
Established in 2019, Versus quickly gained a reputation for a user-friendly UI and intuitive search options. It has gained a lot of users and become a popular marketplace due to its focus on security. Buyers can purchase a range of digital goods and services which include illicit drugs, software and malware, and services related to fraud. The marketplace has over 8,400 listings and 500 vendors who communicate in English and accept Bitcoin for transactions.
White House Marketplace (WHM)
White House Market is a dark web marketplace that enforces the use of PGP (Pretty Good Privacy) encryption to just browse the site. The site goes into detail about its security on the About page and explains that it does not store Monero private keys on their servers, which can ease the mind of its users. Although White House Market is a smaller marketplace than the others on this list, it is possible that its ultra-security features and simple, easy-to-use UI will quickly attract more vendors.
Source: Digital Shadows
Other markets include Icarus market, Dark0de Reborn, Canada HQ, Monopoly Market, and more.
How to Keep Track of Evolving Darknet Marketplaces
There are various active dark web marketplaces. According to Webhose, one of our data providers, there are approximately 20 active leading dark web marketplaces and there are dozens of smaller additional marketplaces.
Gaining access and monitoring these darknet marketplaces comes with a unique set of challenges. Firstly, they generally have short lifespans. This could be for a variety of reasons, for example, law enforcement might close them down, or perhaps to help avoid this fate they frequently change their domain address. It could even be because the admin implemented an exit scam, which is what happened with Empire Market, where the admin team is estimated to have made off with some $30 million worth of Bitcoin in August 2020.
Because of this short lifespan, security professionals need to constantly be on the lookout for the next big marketplace. However, because of the illicit nature of the dark web, many websites don’t want to be found, as such there is no easy way to navigate the dark web. Each website can be thought of as an independent silo. Darknet websites rarely, if ever, link to one another. To find the forums and marketplaces where the important and relevant is you will need to know what you’re looking for and how to look for it.
Finally, once the relevant sites have been located and access gained, there is still the serious challenge of monitoring the dark website to effectively gather usable intelligence. Doing this manually requires vast amounts of resources, however, you also can’t simply scrape the website as such activity can quickly get you banned from a site.
This is where Open Source Intelligence (OSINT) tools like Signal come in.
The Role of OSINT tools when Monitoring the Dark Web
OSINT tools allow security professionals to effectively and efficiently monitor the surface deep, and dark web. Using Signal you can create targeted searches with Boolean logic, and then run the results through intelligent filters powered by our advanced AI. This process can be automated with real-time SMS and email alerting.
This reduces the need for skilled professionals to spend all their time manually monitoring the entirety of the web and assessing the associated risks. Additionally, it reduces the inherent risk of accessing criminal forums and marketplaces. Instead, security professionals get hyper-relevant alerts that can quickly be assessed and acted on without ever actually having to go onto the dark web or painstakingly gaining access to marketplaces.
This approach is vastly more time-efficient and allows you to put your web monitoring on auto-pilot, reducing costs while simultaneously increasing efficacy. As cyber-criminals embrace new technologies it’s becoming increasingly necessary for security professionals to do the same in order to stay ahead.
Increase the scope of your monitoring ability and the overall amount of hyper-relevant intelligence at your fingertips. Gather actionable intel in realtime.
7 Dark Web Forums You Need to Monitor for Improved Cyber Security
We take a look at how security professionals can utilize OSINT tools like Signal to more efficiently and effectively monitor threats on dark web forums.
The dark web has grown in popularity over the years as people become increasingly technologically savvy. Using a darknet browser like Tor or I2P allows users to stay anonymous whilst browsing online.
There could be any number of reasons a person desires anonymity online, and many of those reasons are perfectly legitimate. For example, they might simply have concerns about large companies’ abilities to track their online activity, they might not feel comfortable giving Google all their data. Alternatively, they might live in a place with restrictions on freedom and free speech and necessarily turn to dark web anonymity to access world news or freely share journalism.
However, the same anonymity which protects those people is also a boon for criminals. It allows them to operate across borders, organize crime, and trade in illegal items, both physical and digital. Additionally, any number of topics can be found on dark web forums being discussed, including extremist ideas, hate speech, threats of violence, or even plans for cyber attacks.
It is this broad array of potentially dangerous activity on the dark web which is of concern for security professionals. By monitoring the dark web with OSINT tools like Signal, security professionals can discover exploit kits targeting their organization, get early alerts of data breaches, and even prevent physical attacks on assets or employees.
In this article, we take a look at a few of the more common dark web forums and how security professionals can utilize OSINT tools like Signal to more efficiently and effectively monitor threats on the dark web.
About Dark Web Forums as Data Sources
Because of the anonymity afforded by the dark web, people feel comfortable discussing all manner of things. As such, the dark web, especially dark web forums, is a valuable source of intelligence for security professionals. Monitoring these channels can help expose real and potential threats ranging from planned attacks, both physical and digital, to fraud, data breaches, and more.
Below we take a look at 7 of the largest dark web forums that professionals need to be aware as potential security data sources.
Nulled
Nulled is an online forum board with over 3 million members as of 2020, mostly used by cybercriminals to trade and purchase leaked or hacked information. In 2016 it became known as the target of a data breach which helped law enforcement to obtain information about possible "suspects", who were registered on Nulled.
Dread
Dread is a forum on the darknet that mirrors Reddit’s functionality. It provides the same familiar community discussion boards. The forum takes many ideas from Reddit, such as sub-communities and user moderation responsibilities. The Website manages to mimic this functionality without any JavaScript. The main goal of Dread is to offer a censorship-free forum, but it also offers some services, such as pen testing.
CrackingKing
Cracking King is a community forum that provides tutorials and tools for hackers. Additionally, you can find information about and from data leaks, as well as gain access to their marketplace.
CryptBB
CryptBB, which launched in 2017, started out life as a private English-speaking hacking forum known for its rigorous application policy, only accepting members who passed an interview. They have, however, recently been expanding with a new section of the site for “newbies”.
RaidForums
RaidForums is a site dedicated to sharing hacked databases and tools to perpetrate credential stuffing attacks. They also have an open web version of their site.
FreeHacks
FreeHacks is one of the most popular and one of the largest hacking forums on the web. This Russian community of hackers and cybercriminals gathers its resources to expand and solidify their knowledge base.
HackTown
HackTown is an educational platform. They have numerous courses all of which focus on hacking for profit. The forum aims to educate new hackers and cybercriminals to help them develop their skill sets and successfully pull off fraud attacks, phishing campaigns and more.
Related: How Can 4chan be Used as a Data Source for Security Intelligence?
Key Challenges of Dark Web Monitoring for Security Professionals
Security professionals face a number of challenges when it comes to monitoring the dark web. For a start, there is the sheer volume of posts. With each of these forums and market places operating across numerous time zones, they have continuous activity. The most popular of them get tens of thousands of posts a day. Manually monitoring these sites is just not a feasible task.
Secondly, the more explicit dark web forums and market places will require you to create an account and may even go some way to verifying you have the skills to be allowed in. While the anonymity of the dark web means they likely can’t work out exactly where you came from or what your true purpose is on their platform, those that are interested might attempt to get further information out of you to determine your real identity. When creating an account it’s important to make sure it holds no relevance to any other online account you hold if you want to maintain your complete anonymity and don’t become a target of those same criminals you are looking to monitor.
Once you’re into one of these forums or marketplaces you will then need to remain active on the platform, without arousing suspicion otherwise you could have your hard-won access revoked.
Finally, a lot of hackers on the dark web would be more than willing to turn their talents and attention to you should you accidentally cross them. Some websites will infect your device with malware and any and all links or downloads should be viewed with suspicion. Additionally, if you do click any links you may be taken to the material you don’t want to see that many people would find disturbing. As such, unless you’re confident you can safely and securely navigate the dark web, it may be better to look for safer, more efficient alternatives.
The Role of OSINT when Monitoring the Dark Web
The Signal OSINT platform works by continuously scanning the surface, deep, and dark web. You can create custom searches using boolean logic and select from several data sources. These search results can then be filtered using our advanced AI and natural language processing (NLP) which enable you to search across languages, determine location, analyze copy in imagery, and even assess the emotional intent behind text through our NLP software Spotlight.
The benefits of having a tool like this for monitoring the dark web include efficient continuous monitoring and assessment of a multitude of sites allowing security teams to monitor more of the web to catch more threats faster. Additionally, they can access this data without ever having to hunt down and access the various dark web forums and marketplaces which is both more secure and much more time-efficient.
This approach allows you to leave your dark web monitoring on autopilot and not only effectively reduce costs but vastly increase the scope of your monitoring ability and the overall amount of hyper-relevant intelligence at your fingertips.
Why you Need to Upgrade your Social Media Security
We take a look at why and how attackers target social accounts as well as reviewing some of the current best practices for mitigating the risks.
For organizations, social media is vital for the success of their business. It forms a central part of their efforts to build brand awareness, establish their community, do market research and gather intelligence. However, because of the frequency with which it’s used and the importance of the role it plays, social media cybersecurity threats can have a very tangible impact on an organization through reputational damage, data breaches, or worse.
In a recent survey by Statista, it was revealed that 22% of internet users said that their online accounts have been hacked at least once, while 14% reported they were hacked more than once. Due to the constantly changing nature of technology and trends, it’s difficult to pin down a defined set of best practices.
In this article, we take a look at why and how attackers target social accounts as well as reviewing some of the current best practices for mitigating the risks.
Why Do Hackers Target Social Media Accounts?
A successful account takeover can enable threat actors to achieve a variety of malicious objectives, from the distribution of malware to the spreading of misinformation. Some of the most common uses for a compromised account are as follows:
Continuing the Attack: Generally speaking, most people are wary of random messages from strangers. However, if you can gain access to someone’s account and launch your phishing campaign against their contacts you can leverage the trust already established as a personal contact to dramatically improve the success rate of the phishing campaign. In the case of an organization’s account, these attacks are particularly harmful as they can target thousands or even millions of followers and can come with serious associated reputational damage.
Gathering Intelligence: The actual account takeover might not be the endgame of the attack. Instead by taking over an account, they gain access to intelligence, from an individual's messaging history to extensive personal details on an individual and their contacts.
Reputational Damage: We’ve already mentioned the potential for reputation damage as a by-product. However, there is a chance that reputation damage is the entire objective of the attack. Attackers might have a grudge against an organization or person, for example. Once they have access to the account they could do a range of things, such as posting racist slurs from the account or directly targeting followers through the account.
Credential Stuffing: Many people use the same login credentials across websites. Once attackers have successfully compromised an account, they then attempt logins at other popular websites using the same credentials to see what else they can gain access to. Often the objective is a financial reward.
Blackmail: If embarrassing or damaging information is surfaced through the account attack then hackers are unlikely to miss the opportunity to blackmail the individual or organization to further their other objectives.
4 Examples of Successful Social Media Attacks
LinkedIn Hacked, Exposing 117 Million Credentials
When: May 2016
Tactic: Data Breach, Account Takeover
The 2016 LinkedIn data breach exposed 117 million records of its users including email and password combinations. These were sold on the dark web and allowed hackers to gain access to and control thousands of accounts as well as use the data for credential stuffing.
Vevo Hacked Via LinkedIn Phishing
When: September 2017
Tactic: Targeted Phishing & Malware
In 2017 the streaming service Vevo suffered a breach when one of its employees was phished via LinkedIn. Through this attack, hackers obtained and publicly released over 3TB worth of the company’s sensitive internal data.
HAMMERTOSS Malware
When: July 2015
Tactic: Malware/Data Exfiltration
HAMMERTOSS is a malware which was created to automatically search and extract data from social networks and was controlled by commands posted by attacker profiles. This novel approach to weaponizing social media shows the need to analyze social media as part of the full lifecycle of a cyber attack.
Twitter Bitcoin Scam
When: July 2020
Tactic: Account Takeover
Through a series of targeted phishing campaigns, hackers were able to get access to internal systems and tools at Twitter. They used this access to take control of numerous high profile accounts, including verified accounts such as Kanye West, Barack Obama, Apple, and Joe Biden. The attackers used the platform to Tweet a message requesting Bitcoin be sent to a specific wallet number with a promise they’d return it doubled. In the short time the message was up the attackers collected over $100,000.
6 Quick Tips to Improve your Organizations Social Media Cybersecurity
1. Employ strong unique passwords.
Avoid the risks of credential stuffing by ensuring that all accounts are locked with strong unique passwords.
2. Keep personal and business accounts separate.
Linking personal and business accounts just make it easier for hackers to gain access to both. So, when possible, keep a separate and distinct login and password for both.
3. Restrict access and permissions.
Not everyone needs to have the ability to login to the organization’s social media accounts. Not everyone needs to be able to post, share or send messages through it. Additionally, when an employee leaves make sure to revoke their access to all social media accounts.
4. Be mindful about what you share.
Even harmless posts might unwittingly share sensitive data that could be used by attackers. For example, you might share an employee update, maybe congratulating an employee for having a child, information which could be used in a targeted spear-phishing campaign.
5. Protect the physical access points.
Make sure devices are password-protected, don’t leave USB devices lying around, ensure that wi-fi networks are private and secure. These physical security threats are particularly prevalent currently with many employees working from home.
6. Be wary of third-party apps.
Third-party apps like scheduling softwares are invaluable, allowing you to save a huge amount of time. However, they also provide an additional way for attackers to gain access to your social media accounts.
The Role of OSINT in Securing Social Media Platforms
By monitoring social networks for mentions of your brand and keywords, you’ll know right away when suspicious conversations about your brand emerge. For example, people might be sharing fake coupons or offers, or an imposter account starts tweeting in your name. Using OSINT you can monitor all the relevant activity online regarding your business and quickly identify fraud allowing you to respond to it in a timely fashion.
Additionally, you can use OSINT tools like Signal to monitor not only your social media channels for things like imposters but also for physical threats against employees or branch locations.
OSINT is vital in identifying when one of the above-mentioned risks of social media becomes more than just a threat when it becomes a reality. Being amongst the first to know when something like this happens allows you to respond quickly and effectively.
How Monitoring Current Events Like the 2020 US Election Can Increase Organizational Security
Tensions around the US election are high for both ends of the political spectrum. There has been an increase in polarization and militarization and many Signal customers have expressed concern.
There are numerous threats that could evolve to seriously impact an organization, from natural disasters, to acts of terror, to targeted attacks on executives. Currently though, tensions around the US election are high on both ends of the political spectrum. There has been an increase in polarization of political views and even militarization of the public in recent months, and many Signal customers have expressed concern.
For many American’s this is seen as the most important election of their lives so far. Fears of voter fraud and voter suppression are rife, which is reflected by an unprecedented number of early votes being cast with more than 90 million votes already cast a week before the election, more than two-thirds of all the votes cast in 2016.
This, paired with a deadly pandemic and a summer of protests, many of which became violent, and one can see the potential for civil unrest around a contentious presidency. To mitigate this risk organizations need relevant intelligence as events unfold to ensure they take the necessary precautions to protect their employees and assets.
As such, we have created advanced tools to enable Organizations to be alerted as early as possible to issues and current events, such as the Election, where the possible fallout could have an impact on their employees and assets.
Monitoring Election Threats in Real-Time Using Signal OSINT
Using Signal security teams can learn of events as they are happening or even before they happen, allowing effective response plans to be enacted, effectively neutralising potential threats.
To do this users can create custom searches using Boolean Logic to filter intel from key web sources such as social media, the open web, and the dark web. Intel from these sources often acts as an early indicator alerting Signal customer to potential issues in real-time. The data can also be reviewed by our emotional analysis solution for increased data analysis efficiency.
Signal has real-time SMS and email alerting for high-risk threats so that companies can maximise available response time. Once alerted to potential risks the security team can form a final judgement on the threat level and decide whether action needs to be taken.
Final Words on Threat Monitoring with Signal
Threat monitoring isn’t just for events such as a contentious election. COVID-19, earthquakes, storms and other extreme weather events, and even threats of violence against specific executives, can all affect an organization. Signal OSINT software enables security teams to scan a vast number of surface, deep, and dark web channels and sources to gain real-time data on a broad array of emerging threats.
Anonymous social media forums like 4chan or dark web forums are often where threat actors go to communicate and organize. And social media is often where you can learn of current events as they unfold. So whether it’s customer data for sale online, or an active shooter situation in-store, security teams armed with OSINT can quickly assess and respond appropriately to mitigate risks and damages.
Only when an organisation has a complete picture that incorporates the variety of potential risks and has invested in specific responses and contingency plans can it adapt as needed to mitigate the impact of extreme events.
LERTR: Advancing Data Breach Detection
Organizations need intelligent security practices and cyber habits if they want to mitigate potential damages through early data breach detection.
As threat actors continuously challenge the cyber defences of organizations, companies are increasingly forced to focus on improving cybersecurity practices. However, even the best cybersecurity teams with the largest budgets find it hard to stay ahead of the evolving threat landscape. And with more technology in use, a growing reliance on cloud storage and the Internet of Things (IoT), there is a growing potential for sensitive data to be exposed to threats.
As such it’s unsurprising that data breaches, in spite of increased cybersecurity spending, are becoming more common and more expensive to deal with. Employees need intelligent security practices and cyber habits and companies need to be armed with the latest technology and tools for early data breach detection to gain the upper hand when combatting this ever-changing threat.
Data Breaches Need to be Caught Early
The average cost of a data breach in 2020 according to the IBM / Ponemon Institute report was $3.86 million. However, there are plenty of examples where the costs have vastly exceeded this average, escalating into the hundreds of millions or even billions. For example, the Equifax data breach in 2017 cost Equifax $1.7 billion in the end. Another high profile example, Facebook eventually settled on a fine of $5 billion after it’s ‘privacy misstep’ involving Cambridge Analytica. This bill doesn’t include the additional costs and expenses that Facebook has accrued in the development and expansion of their cybersecurity and privacy departments nor does it account for the reputational damage it suffered.
While costs of these extremes are rare, data breaches in general are not. The IBM report goes on to analyse particular subsets of the data noting that the worst impacted is healthcare with an average data breach cost exceeding $7 million. And that the average time taken for an organization to identify and contain a data breach, was an astonishing 280 days, over 9 months. This is in spite of significant evidence that the speed of containment has a significant impact on the overall data beach cost, which if left unchecked can linger for years after the incident.
How to Prevent Data Breaches
As with many of these things prevention is often the best policy.
Data Breach Prevention #1: Have Clear Security Protocols
Every employee should know, understand and be able to abide by strict security protocols to keep company data secure and thwart social engineering tactics. Having protocols is one of the best ways to help prevent data theft by ensuring unauthorized personnel do not have access to data.
Data Breach Prevention #2: Safeguard Against Human Error
Many data breaches are the result of an employee error. This could be anything from downloading a document off of an illegitimate website, social engineering tactics or even outright blackmail. Employees should only have access to the information that is vital to their particular roles within the company. Those with higher level access should accordingly have higher levels of cyber security training and understanding.
Data Breach Prevention #3: Improved Password Protection
Having strong unique passwords is the first line of defence against any cyberattack. However, nobody, whether they are a high level executive not, is going to be able to remember a dozen or more 12 character passwords that use special characters, letters and numbers. Make sure that 2FA is enabled on all logins, and use a password manager (with 2FA enabled) to auto generate and save complex passwords and ensure the highest levels of password security are enabled.
Data Breach Prevention #4: Update Security Software Regularly
Companies should utilize a high quality antivirus software, anti-spyware program and firewall. Additionally, these programs should be regularly updated to keep them free from vulnerabilities.
Data Breach Prevention #5:OSINT for Dark Web Forums
By monitoring dark web forums and other chat rooms you can learn of planned attacks, potential exploits and even find exploit kits being sold online. This will give you a good indication of the access methods which have been discovered allowing you to implement a patch quickly to prevent it.
The Tools for Early Detection of Data Breaches: LERTR
Having the right tools is vital if an organization wants to prevent or mitigate the threat of data breaches. Using an OSINT platform like Signal allows security teams to efficiently monitor the surface, deep, and dark web for details or indications of potential and past data beaches. For example, you might find exploit kits targeting a vulnerability specific to your company. This would allow you to prepare a patch for this vulnerability before it was exploited.
Additionally, hackers might discuss strategies or plans around an upcoming data breach attempt on a dark web forum. Forewarned, you have a better chance of catching and preventing the attempt. However, prevention isn’t always possible. For those scenarios where you do face a data breach you want to discover it as quickly as possible to mitigate the potential damage and limit the costs.
To this end we have integrated with Webhose to advance our early data breach detection capabilities. Additionally, we have launched LERTR, a cyber specific OSINT platform. aa
Automate Intelligence
With powerful tools at hand you can spend less time searching data and more time planning and implementing responses.
Be the first to Know
Defend against future attacks with relevant actionable intel. And be the first to know about compromised data, control damages.
Better Risk Protection
With improved risk protection you will be the first to know if an event that threatens your brand occurs enabling you to stay ahead.
Final Words
Data breaches are increasingly common and expensive. Effective preventative measures need to be put in place and maintained to limit threats. However, even the best defences can fall to a determined threat actor. As such organizations needs to ensure they have all the tools to not only prevent, but also to detect early and contain data breaches quickly should one occur.
Signal is a powerful OSINT tool which allows users to create searches using boolean logic enhanced with NLP, with which security teams can efficiently monitor online activity to detect threats as or even before they emerge.
5 Ways AI is Subtly Shaping the World as we Know it
AI is shaping our world in numerous ways from targeted ads to rapidly advancing facial recognition applications and even AI-generated malware.
Artificial Intelligence (AI) describes technologies that can make informed, non-random decisions algorithmically. It has many current and potential applications, it is the current pinnacle of humanities ceaseless drive towards greater and greater efficiency. In particular regard to OSINT though, it enables humans to collect, analyze and interpret huge sets of data, data sets so large that it would be entirely unfathomable to even approach them without machine assistance.
Everyone knows AI is shaping their world in one way or another. But often the changes are subtle, gradual and go unnoticed. Very few of us know what actually goes on behind the steel doors of the big tech companies like Alphabet, Facebook, and Apple. And yet we interact with their AI systems on a daily basis and those systems have huge power over our lives. In this article, we take a look at some of the key ways AI is being used today and how it will become increasingly important as our technologies improve.
5 Ways AI is Shaping the World
1. Improving and optimising business processes
The very first robots in the workplace were all about automating simple manual tasks. This is the age of factories and production lines. Today though, it’s not manual tasks that robots are taking over. Instead, software-based robots are taking on repetitive tasks carried out on computers.
Initially, this was limited to automating simple repetitive tasks, such as “send follow up email 2 if no response after 3 days”. This has already reduced admin tasks and improved business operational efficiencies immeasurably. The next step though is the use of AI technologies to further alleviate some of the more labour intensive ‘intelligent’ tasks such as data gathering, aggregating and analysis, leaving people to spend more time on complex, strategic, creative and interpersonal tasks.
2. More personalization will take place in real-time
Big tech companies are already using data to personalization services. Google Discover, for example, is a feed based on a complex algorithm which reads your online history and tailors the news feed to your particular interests. Other big tech examples are Spotify and Netflix which use AI to suggest relevant media based on your historical behaviour.
This technology is constantly being evolved and is probably one of the most noticeable in our day to day lives. The end goal is a system which can almost perfectly predict your desires and needs, an outcome none of us are likely to protest against. On the other side of the same coin though is the use of that very same data to target individuals with hyper-relevant ads. This practice can often seem intrusive and is one of the driving forces behind the adoption of VPN’s.
3. AI in the creative space
Some things are still, even in 2020, better handled by humans. That being said AI technologies are now beginning to encroach on the creative spaces. Scorsese's, The Irishman, is one example of this, where Robert De Niro was de-aged on-screen using AI technology.
There are additional uses though, for example, AI is being used to edit video clips for the purposes of spreading misinformation, and often these edits are incredibly hard to spot. This has led to a new sector of cybersecurity which requires AI technology to spot AI-generated or edited video and audio files.
4. Increasing AI in Cybersecurity
Even as data grows and is used to progress the development of AI this simultaneously opens up new avenues for exploits by threat actors. For example, AI can be used to create and automate targeted ‘intelligent’ phishing campaigns. AI-supported cyberattacks though have the potential to go much further. As such, increasingly advanced AI is needed to combat the evolving cyber threat landscape.
Related: How Machine Learning is Changing Modern Security Intelligence
5. AI learning to perfectly emulate humans
Anyone that keeps their eye on the work that Google is doing will know about their 2019 update, BERT. A natural language processing (NLP) framework which is designed to better understand context and intertextual reference so that they can correctly identify both the searcher's intent as well as the intent behind any content created.
One of the key challenges that faces AI right now is idiomatic or referential speech; language that has more depth of meaning, for example, determining the importance of the concept of a mother, or understanding a phrase like “six feet under”. Our current research and development project at Signal is one example of the practical applications of overcoming this challenge. It involves using machine learning to enable our software to understand the intent behind text, even when ‘hidden’ behind challenging language like idioms, to more accurately identify threats.
As these natural language processes advance, so too will conversational AI bots, to the point where, because of the range and complexities of their answers, you would be forgiven for mistaking them as human.
The Future of AI and what that means for OSINT
Artificial Intelligence, machine learning, and automation have already revolutionized intelligence gathering. With OSINT tools like Signal security teams and intelligence agents can effectively and efficiently monitor the open, deep, and dark web, setting up customized alerts based on searches that leverage boolean logic. Machine learning takes this intelligence to the next level. It allows for vast amounts of data to be collected, aggregated, and for all the irrelevant hits to be essentially culled, supplying the security team at the end with actionable, relevant intelligence.
Humans play an essential role in this new intelligence lifecycle. In defining the search terms to match security strategies, analysing the end date the system feeds back, reassessing the searches based on the new evidential data and implementing appropriate responses. This is a key role that will no doubt evolve as the technology becomes more accurate, reducing inefficiencies in process.
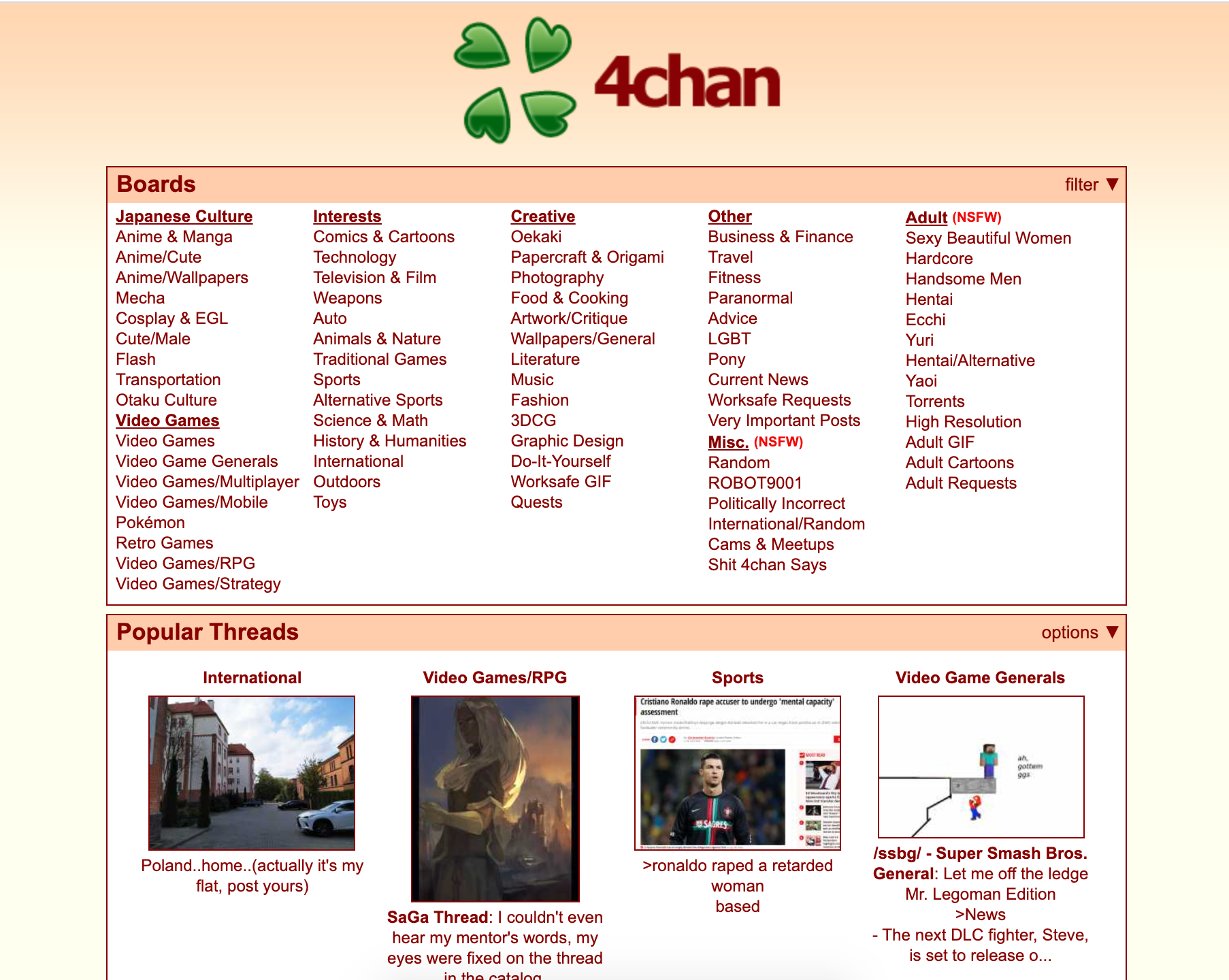
How can 4chan be Used as a Data Source for Security Intelligence?
4chan is just one of the data sources you can monitor using Signal. You can find conversations by alt-right groups, threats of violence against a person, organization or group, and more, which makes it a valuable data source for security professionals.
What is 4chan?
4chan is one of the largest English language based image boards on the open web. They have over 900k new posts per day and some 27 million active monthly users.
What makes it a unique social platform is that users can choose to remain anonymous. They don’t even need to create an account to access and engage with content on the platform. As an added security measures, posts time-out after a period so they can’t, unless found and archived by an independent data gathering source, be checked and referenced by security teams, users, or law enforcement at later date.
There is a wide range of topics hosted on the platform, from Japanese culture, to politics, to adult content. Because of the anonymity allowed, as well as a very limited moderation by the site owners, 4chan has a large amount of illicit content and activity. This activity includes cyberbullying, child pornography, harassment, violent threats, racism and extremist ideologies.
Despite this, it’s important to note that there is nothing inherently bad about the platform, just as there is nothing inherently bad about the dark web, and many of the users use it for legitimate purposes such as for its original intent which is the exploration and discussion of the Japanese film and television animation style, anime. In fact, like Reddit, many influential memes have originated from the platform such as ‘lolcats’ and ‘chocolate rain’. As such it has historically been an important driving force behind the development of internet culture.
Bottom line: 4chan is a forum, the original purpose was for the discussion of anime and Japanese culture. It’s a forum where users don’t need to have an account or sign up with a name, there is little moderation, and posts are deleted from the server after a period, as such there are few consequences. With this format, people can and do say just about anything on the platform.
How can 4chan benefit your organization as a data source?
The anonymity offered by the channel means users feel comfortable talking openly and they do so around a wide range of subject matters and people. For example, under the political forum /pol/ you can find examples of alt-right groups, threats of violence against a person, organization or group, and racist behaviour.
The range of topics discussed and the freedom with which individuals and groups openly discuss them can give security teams and law enforcement an idea of emerging trends as well as be one of the first places that death threats or threats of violence against individuals and organizations can be found. In the past, terrorist manifestos have also been posted on the channel. These discussions can indicate when an event is going to evolve into a tangible threat and give security teams a heads up to prepare and mitigate the potential threat.
Additionally, there are groups and individuals on the channel, such as the members of Anonymous who have turned their online attention, for right or wrong, to intelligence gathering on people and organizations. Often, 4chan is one of the first places they share their findings. For example, they might uncover and share personal details about a CEO such as their address, medical records and details of their family.
Why use Signal for monitoring 4chan?
One of the key problems with any form of online intelligence reconnaissance is the quantities of data you need to assess to get even the smallest tidbits of potentially useful information. 4chan has this problem in spades with over 3.5 billion posts. And these posts are transient, with the more R rated the post being the shorter it’s existence. This means relevant security intelligence on the 4chan platform might only be public for a couple of days. To gain real insights into the channel you need to be constantly and efficiently monitoring with real-time alerts.
4chan is just one of the data sources you can monitor using Signal though. You can simultaneously monitor the open, deep, and dark web including forums like Reddit and chatrooms like Telegram. Our system allows you to create tailored keyword-driven searches with boolean logic which is assisted by our machine learning and language processing AI to efficiently gain intel on hyper-relevant, new and emerging threats.