7 Growing Cybersecurity Threats Professionals are Increasingly Worried About
We take a look at 7 of the growing concerns that cybersecurity and infosec professionals have as the trend towards digitizations continues at an increasingly explosive pace.
The new softwares and systems that are employed across an organization create new attack vectors for threat actors and new data security concerns. Not only that but as these new digital systems are put into use to replace once manual tasks additional complications arise from potential user errors, for example, an employee might make private data public without even realising.
In this article, we take a look at 7 of the growing concerns that cyber and infosec professionals hold as this trend towards digitizations continues at an increasingly explosive pace.
1. Unintentional Data Exposure
“To err is human,“ as Alexander Pope famously wrote. We all make mistakes and to combat this we have progressively leveraged more technology across industries to automate processes and reduce the potential for human error. However, technology can’t prevent our every mistake, and paradoxically, this use of technology increases the amount of data we as people and organizations produce and store in our systems. Hackers are aware of this and continue to find creative ways to exploit human weakness with strategies such as complex phishing campaigns.
On top of this, the adoption and rapid development of hardware (phones, for example) mean many people conduct work from their personal mobile device. And the move towards work from home driven by the COVID-19 pandemic has furthered this merger of work and personal devices as well as increased the amount of work done from unsecured networks.
2. Adoption of AI into Malware for Scale and Evasion
Denial of service attacks can take a variety of forms, from malware to DDoS attacks, and have huge financial implications for an organization. In 2018, for example, shipping giant Maersk had their IT systems taken out by a vicious malware called NotPetya, costing them an estimate $300 million.
These ransomware attacks might be driven by political motives, thoughts of financial gain, or something else entirely. Over the last few years, these tactics have evolved they’ve adopted new technologies and strategies allowing threat actors to increase both the scale of the attacks, as well as to more effectively neutralize increasingly complex security protocols.
One increasing concern is the adoption of AI into these attacks. AI can be used in a variety of ways, such as increasing the effectiveness of phishing campaigns. One example was developed by IBM Research, DeepLocker. DeepLocker hides its malicious payload in benign carrier applications, such as a video conference software, to avoid detection by most antivirus and malware scanners and then uses facial recognition to identify the specific target and launch its payload.
How AI is used to could completely change the way information security and cybersecurity professionals, in general, need to adapt and respond to threats.
3. Financial Fraud
Financial fraud off the back of data breaches is nothing new. However, it continues to be a problem today and into the foreseeable future. Data breaches from large organizations, whether they are related to your organization or not could easily lead to new attack vectors on your company.
There is a huge amount of Personal Identifiable Information (PII) for sale on the dark web. This data can be used in a number of ways, from credential stuffing strategies to identifying high-value targets and refining strategies for spear-phishing campaigns.
4. 3rd Party Integrations
Often organizations spend a huge amount of time and money ensuring their internal cybersecurity practices are excellent. It only takes one breach to realize the efficacy of this investment. Successful ransomware, for example, against an organization for example could cost tens of millions not even considering the reputational damages that might accompany the financial ones.
However, as was seen with the 2020 SolarWinds breach, it doesn’t matter how well educated your staff, how up to date your firewalls, how alert your security teams are if your third party integrations have weaknesses.
5. Increasing Amounts of Sensitive Data Collected Through IoT Devices
Internet of Things (IoT) devices is beginning to infiltrate every level of our lives. From mobile robots, to inventory tracking, to personal assistants, connected speakers and smart TVs. These devices seek to automate and simplify our lives.
However, what many people don’t realize is that these machines are often insecure by design and offer attackers new opportunities. Additionally, the terms and conditions around data sharing and usage from many of these devices lack transparency, and by utilizing this technology an organization makes it increasingly difficult to know and control what data is going out.
Finally, it’s often the case that, while a vendor may recommend applying new firmware updates, they are not applied unless the device starts misbehaving and someone applies the update to troubleshoot the issue. This could lead to serious security compromises.
6. Rise of Fake Online Personas
This threat can have a direct and dramatic impact on organizations reputation and the physical security of employees. By creating and leveraging fake or phantom social profiles threat actors can create trending news and information, promote poor products, or push lies and deceptions to further an agenda.
The application for these kinds of campaigns is vast, affecting everything from national elections to company sales and share prices, and there is currently no system in place to identify false profiles efficiently and counter the purposeful spread of misinformation in this way.
7. Shortfall of Professionals
The final security risk on the list is the continued shortage of skilled security workers. As cybersecurity threats evolve, and areas such as information security become more important for organizational security, increasing numbers of skilled and trained professionals will be needed.
Finals Words
Many people are now desensitized to the fact their data is shared online either through breaches or loose company policies. Because we cannot regain our privacy, they often become careless about protecting it further. Add to this the constant evolution of cybersecurity threats, and the challenge for cybersecurity professionals looks like a tough one.
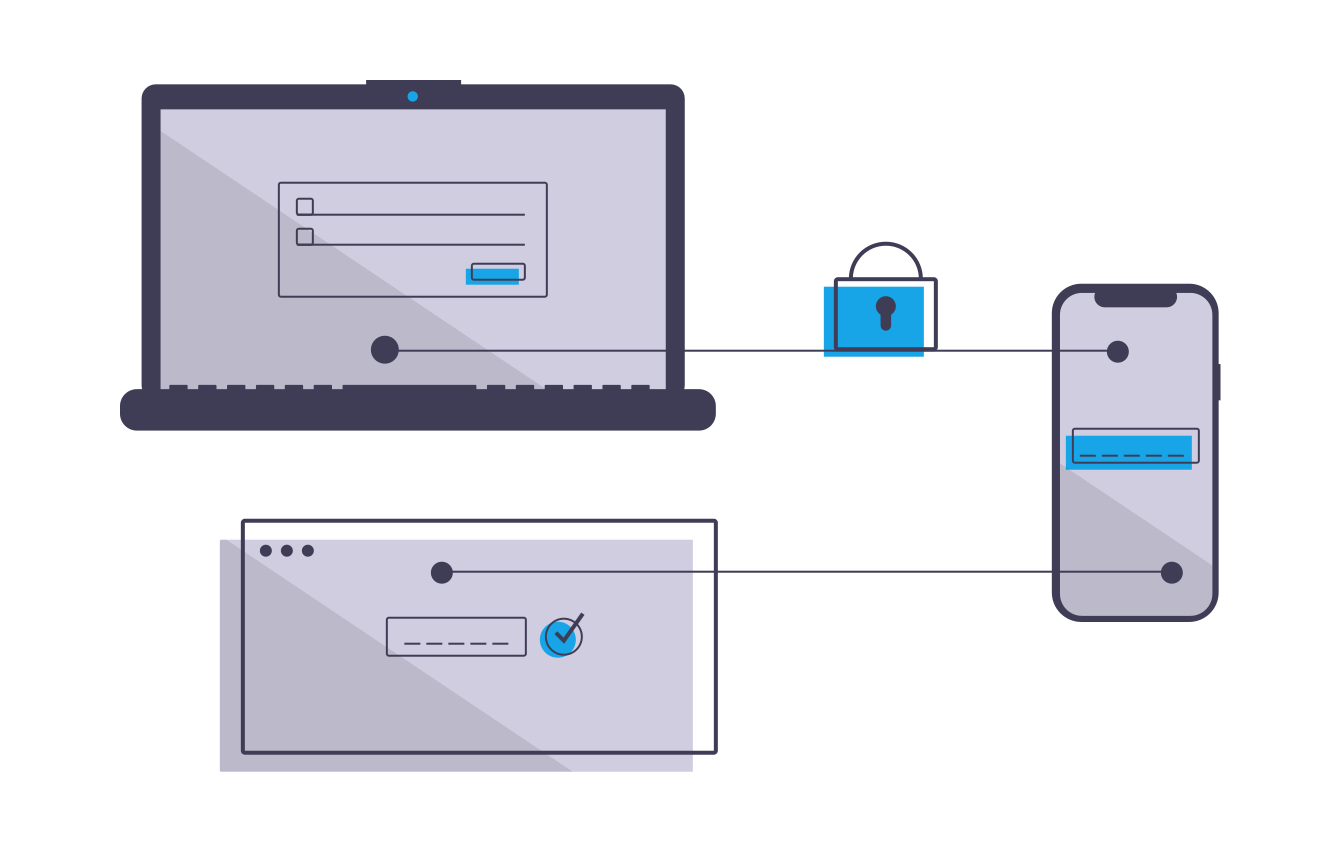
To ensure organizational security, companies need a combined response, that includes continuous education of employees, restricted accesses, and multi-factor authentication. This needs to be paired with a skilled security team who are armed with the necessary knowledge and tools such as OSINT software.
Security professionals need to be able to gather real-time data on emerging threats and proactively implement an effective response.
The Threat of Doxing to Organizational Security
Organizational doxing is on the rise and can be immensely damaging, exposing company secrets and customer data, or more directly exposing executives to new levels of threats.
What is Doxing?
The term itself originates from the phrase “dropping docs” and was later shortened to “docs” and then “dox”. As the original term suggests, doxing is when someone collects and then shares information about another person or organization.
There are numerous reasons someone might dox someone else or be the victim of doxing. It could be for revenge or a personal grudge, a disgruntled ex-employee might target their previous employer, for example. In 2014, Sony was the victim of a doxing attack backed by, experts believe, the North Korean government after they released a film which made fun of their leader. Other motivations include harassment and cyber-bullying, vigilante justice (for example, exposing neo-Nazi’s), and doxing for financial gain.
Organizational doxing is on the rise and can be immensely damaging, exposing company secrets and customer data, or more directly exposing executives to new levels of threats.
Doxing Strategies and Goals
Traditionally doxing started with an online argument escalating to one person digging out information on their adversary and sharing it online. More recently though, doxing has become more of a cultural tool with hackers taking down people or groups with opposing ideologies. When it comes to organizations, threat actors have been known to both target an organizations reputation and to use information gained through a doxing attack to leverage financial reward.
For example, in one scenario an employee at a bank was blackmailed after a doxing attack into using his position in the bank to steal over $100,000 from customers for his blackmailers.
The fallout is generally reputational with the victim suffering from online abuse such as death threats to them and their family in lieu of the new information shared. However, on occasion, the fallout can be significantly worse. There have been examples of mobs dishing out physical vigilante justice after a person's information, such as an address, was shared online.
There are numerous ways you can be identified online. By following ‘breadcrumbs’ of information a dedicated doxxer can assemble an accurate picture of a person - even if they were using an alias. The kind of details they might look for include, full name, current address, email address, phone number etc. Additionally, some doxxers might buy information from data brokers.
IP/ ISP Dox
There are various methods that can be used to locate your IP address, which is linked to your location. With just your IP address a doxxer could then use social engineering tactics against your Internet Service Provider (ISP) to discover the information they have on file such as:
Your full name
Email address
Phone number
ISP account number
Date of birth
Exact physical address
Social security number
This requires the doxxer to go through a dedicated process, which may not even work, however, it’s just one strategy they can employ, and even if they are unable to gather further information through a gullible ISP worker they still have the first parts of the puzzle - your IP address and a rough location.
Doxing with Social Media
If your social media accounts are public then anyone can view them. Often things a threat actor can find out include your location, place of work, your friends, your photos, some of your likes and dislikes, places you’ve been, names of family members, names of pets, names of schools you attended, and more.
With this kind of information, they can then find out even more about you, or even discover the answer to your security questions helping them break into other accounts such as your online banking.
As such it’s recommended to keep your social media profiles private, and if you use multiple online forums to use a different name and password for each to help prevent doxxers from compiling information from across multiple online forums and social media sites.
Data Gathered through Brokers
Data brokers on the internet collect information from publicly available sources and then sell the data for profit. Generally speaking, they sell this data to advertisers - if you’ve ever found yourself randomly receiving emails from companies you’ve never heard of before, this is why. However, for a doxxer it could be an easy way to start building a detailed profile of their target.
How Might Doxing be Used Against Your Organization?
For organizations to be successful with their media strategies they necessarily need to share relevant information and regularly engage with their customers through social media channels. This provides a substantial opportunity for doxxers.
By combining publicly-available data with basic attack techniques, such as phishing campaigns or credential stuffing, malicious actors can uncover large quantities of supposedly secure data. For consumers, exposed information could lead to identity theft or public shame. Meanwhile, companies face the prospect of large-scale reputation damage or lost revenue if proprietary project briefs or intellectual properties are leaked to the public.
Additionally, doxing can be used as an incentive to expedite the resolution of ransomware attacks. This is where the cyber attacker threatens to release documents or information to the public should their target not pay the ransomware fee promptly. This adds to already serious financial implications.
How Can you Prevent Doxing?
Unfortunately, it's nearly impossible to completely remove personally-identifying information from the internet, especially parts which are part of public records. Still, there are some tips to reduce your attack surface.
Keep your profiles private
People and organizations do have a lot of say as to what gets published on the internet. Make sure to practice general data privacy best practices.
Avoid posting identifying information
Keep all social media settings at the most private level, and don't accept friend requests from people you don't know
Change the settings on Office and your phone's photo app so personal info isn't embedded in those files
Use a "burner" email address for signing up for accounts when possible.
Set the ‘whois’ records on any domains you own to private
Ask Google to remove personally available information about you, and request the same from data broker sites
Implement Safe Browsing Measures
These steps are good internet hygiene in any case, but can also prevent a breach that can lead to your info being exposed to a potential doxxer:
Use a VPN, especially when using insecure public Wi-Fi networks
Switch to a secure email system with built-in encryption
Vary your usernames and passwords
Self-Doxing
Humans remain the weakest link in the security chain. In most cases, malice isn’t the problem or the intent when someone lets a threat actor in. Instead, employees overshare personal data on corporate platforms by accident or use insecure third-party applications. In both cases, however, following the breach and identifying the potential compromises is difficult when IT teams start from the side of defenders.
By flipping the script and looking at your organization from the view of potential doxxer it becomes easier for IT and security teams to spot key areas of weakness. They can then develop strategies and staff training programs to protect against them.
Final Words
Doxing represents a growing threat to organizations and individuals. However, by self-doxing with security intelligence gathering strategies, security teams can create accurate attack surface maps. With this intelligence, they can then enhance threat modelling and deliver actionable insights to staff to reduce overall risks.
Using OSINT software like Signal you can learn about potential threats as or before they occur, learn about potential exploits targeting your organization, and self-dox to help identify weaknesses and shore-up defences.
Why organizations need threat intelligence tools as part of their security defences
Threat intelligence is an essential tool for any security team. It is the gathering of evidence-based knowledge to inform action-oriented preventative and reactionary responses to an ever-evolving cyber threat landscape.
What is Threat Intelligence?
Those very same technologies that have allowed globalization, which have brought us all closer together and enabled organizations and brands to achieve the current growth and success they enjoy today, have simultaneously brought with them increased risks. These risks come in the form of increased vulnerabilities and exploitable attack vectors for cyber attackers. Threat intelligence is all about gathering data and knowledge to combat and mitigate these threats.
Threat intelligence provides organizations with information and context required to effectively predict and even prevent cyberattacks. Additionally, it helps inform security teams of the best practice for both preventative measures and response measures to ensure if there is a cyberattack the resulting costs are minimal.
In short, threat intelligence is the gathering of evidence-based knowledge to inform action-oriented preventative and reactionary responses to an ever-evolving cyber threat landscape.
The Importance of Threat Intelligence
Threat actors are increasingly persistent, and their persistence pays off. Even the most dedicated professionals can’t help but struggle to keep abreast of every new cybersecurity development. New exploits are constantly being discovered or developed and strategies such as social engineering are increasing in complexity. Security teams need up to date data and intelligence on evolving threats if they are going to be able to develop effective responses.
Additionally, within the corporate world one of the key buzzwords of the last two decades has been “accessibility”. Accessibility to data means organizations have necessarily become reliant on digital processes and almost everything is stored on the cloud. Unfortunately, while accessibility is essential to developing efficient processes, and effectively using big data, it also increases the number of threat vectors that attackers can exploit. According to the IBM 2020 data breach report the longer a data breach goes undetected the more expensive it ends up being for the organization. Primarily then, threat intelligence gathered using tools like Signal OSINT can help organizations detect data breaches earlier, mitigating the eventual costs both reputational and monetary.
The final reason that threat intelligence plays such a pivotal role in today’s security is the distinct lack of skilled cybersecurity professionals. Threat intelligence is a time-consuming business that requires a skilled deft hand to manage. The best threat intelligence solutions use machine learning to automate data collection, then filter and structure data from disparate sources to present only hyper-relevant information to a skilled security team for final analysis. The security team can then use this data to create effective actionable plans based on evidential knowledge. This approach optimizes the performance of both the cybersecurity professional and the intelligence tools being used.
Threat intelligence is actionable — it’s timely, provides context, and is able to be understood by the people in charge of making decisions.
Use Case Examples for Threat Intelligence
Threat intelligence can be used in a diverse range of strategies which makes it an essential tool for security teams in any organization. It’s most immediate value is in helping prevent an attack by gathering intel on threats in real-time, however, it’s also useful for a broad scope of activities such as managing vulnerabilities, informing decision making, and responding to attacks as or after they happen.
Related: The Role of Threat Intelligence and Cybersecurity in Retail
Prevent an attack
From the time that a vulnerability is found to the time an exploit targeting that vulnerability is available for threat actors is shortening. Security professionals need to know about the vulnerability fast so that they can implement a patch and prevent it from being exploited.
Respond to a Data Breach
Data breaches are costly and often go unnoticed. With the right threat intelligence tools you can determine when a data breach happens fast and take suitable actions to mitigate the costs of any following repercussions.
Manage a Vulnerability
The approach of “patch everything, all the time” is impractical and will likely see organizations fall behind - leaving more serious vulnerabilities open for longer. Threat intelligence can help security teams effectively manage vulnerabilities by giving the salient data to allow them to prioritize patches based on actual risk.
Risk Analysis
This leads on nicely from the last point. Threat intelligence can help security teams determine the actual risks associated with potential vulnerabilities or attacks by providing additional contextual information. For example, threat intelligence can help security professionals answer the following questions:
Which threat actors are using this attack, and do they target our industry?
How often has this specific attack been observed recently by enterprises like ours?
Which vulnerabilities does this attack exploit, and are those vulnerabilities present in our enterprise?
What kind of damage, technical and financial, has this attack caused in enterprises like ours?
Fraud Prevention
Fraud can encompass anything from a fraudulent use of your brand, data, or even impersonation of your employees. For example, an individual might impersonate a doctor and sell fake versions of your prescription medication online.
Incident Response
Having the ability to gather and filter through threat intelligence from across the surface, deep, and dark web in real-time allows security teams to effectively and appropriately respond to incidents as they are happening.
How can Signal threat intelligence improve your organization’s security?
Signal allows our customers to analyze emerging global trends, detect threats in real-time, and then form appropriate security strategies to counter these potential threats as or even before they fully reveal themselves.
One of the key issues that security teams and analysts face is the sheer amount of noise that might surround their brand. Invariably much of this noise is irrelevant to their purposes, however, some of it will be bad. This is why Signal assists with advanced filters with boolean logic as well as features such as our emotional analysis tool.
How Can Organizations Combat Increasing Cybersecurity Gaps due to Remote Working During COVID-19?
The security challenges of working from home are enormous and are invariably compounded by technological difficulties and poor home security practices.
Whether they like it or not, many organizations have been forced to adopt work from home practices to continue operating. Working from home isn’t new. In fact, between 2005 and 2017 the numbers of people that were able to work from home grew 156%. However, it has generally been seen as a bonus rather than a given and more traditional workplaces have been resistant.
Despite the fact that 49% of office workers have never experienced working from home before, this experiment has largely been a success. Empowered with communication tools like Slack, Microsoft Teams, Google Hangouts. and Zoom, teams have had deep connectivity even from their own living rooms and many organizations have actually seen increased productivity.
Even so, the challenges of working from home are enormous and are invariably compounded by technological difficulties and poor home security practices.
Security teams, in particular, are feeling the pressure. With numerous workers now operating outside the corporate network security controls, new attack vectors have been opened up which are being exploited by cybercriminals.
Cybercriminals Taking Advantage of the Pandemic
Several security providers have put together data sets which show clear spikes in malicious activity since the beginning of the pandemic. McAfee created its own coronavirus dashboard which shows malicious detections quickly growing from the hundreds into the thousands over the last six months. The most common threat type has been Trojans with Spain and the US being clear outliers in the number of threats detected.
As of August, there were nearly 2 million malicious detections against over 5,500 unique organizations. McAfee go into detail about the families and types of attacks that they’ve seen a spike of cases in since the pandemic began.
WFH challenges for security teams
We’ve established that cybercriminals are taking advantage of the security breaches created by a sudden adoption of working from home but what is it exactly that makes working from home lees secure and what exactly are the security flaws threat actors are targeting?
Working from home doesn’t necessarily mean working from home, it could also mean working from anywhere and many workers have already figured that out. This means workers can (in theory) escape their houses and head out to cafes, restaurants, libraries or other public spaces with free WiFi networks. Zoom, with its virtual background feature, has incidentally supported this. The key issue with this is when workers operate on unsecured open networks.
Ultimately security professionals have to try and ensure device security and data protection in the work from anywhere model - a challenge made significantly harder with over 50% of employees using their own devices during this period. IT teams have tried to make the security transition easier, with some 70% increasing VPN use among employees, however, 1 in 4 workers according to the Morphisec report were unfamiliar with their company’s security protocols.
This challenge for security professionals has resulted in the majority of security professionals seeing a sizeable increase in workload since their companies began corporatewide remote work. And while most of the transition to WFH went smoothly, respondents reported an increase of security incidents, with the top issues including a rise in malicious emails, non-compliant behavior by employees and an increase in software vulnerabilities.
What can be done to improve WFH security?
Security teams have had years to develop best practices for combating the ever-evolving cyber threat landscape. The sudden move to work from home though has shifted power away from them and brought a greater reliance onto workers who simply do not have the expertise to maintain proper cybersecurity protocols.
Worryingly, 20% of workers said their IT team had not provided any tips as they shifted to working from home. This has opened exploitable attack vectors and introduced new challenges for security professionals. This though isn’t to say that there is nothing that can be done.
Step 1: Control the WFH Environment
This is all about educating employees about best practice and the reasons for these practices when working from home. For example, informing them not to use open networks.
Step 2: Control the WFH Computer
It’s a good idea to supply the computer being used so that you can install the proper security softwares and control access to sites which might offer security risks as well as maintaining control over permissions.
Step 3: Improve your Phishing Responses
The crossover between home life and work life extends beyond the location. People are more likely to spend time on social media networks and working on private projects than they would be if they were in the office. This opens them up to more phishing campaigns so it’s important they know how to avoid falling for them.
Step 4: Restrict Remote Access to Sensitive Documents and Data
Lockdown permissions and access to sensitive documents and data. If they really need access they can communicate this need with you directly and you can ensure it is done securely and safely.
Step 5: Monitor Surface, Deep and Dark Web for Emerging Cyber-Threats
Use an OSINT tool like Signal to monitor for cyber threats, planned attacks and data breaches.
Step 6: Encourager VPN Usage
VPNs are a simple and easy way to improve security. It’s worth ensuring the company has a quality VPN service that doesn’t slow a users internet connection unnecessarily as this might persuade workers to turn it off.
Step 7: Don’t Allow Split-Tunnels
Split-tunnelling allows a user to access networks through both the encrypted VPN service and a potentially unsecure network simultaneously.
The Role of Threat Intelligence for Improving Work From Home Cybersecurity
One of the key benefits of using an OSINT solution like Signal is the ability to create customized searches with Boolean logic to uncover hyper-relevant threats in real-time with SMS and email alerts.
Ways that this has been used in the past to improve cybersecurity include:
Early detection of data breaches. The average cost of a data breach in 2020 is $3.86 million. The earlier you catch a data breach the faster you can take action to mitigate the associated financial and reputational damage.
Discovery of new cyberattack strategies, exploit kits, phishing tactics which were talked about or for sale on the dark web.
Organizations have uncovered attacks that are yet to be carried out. This is true for both physical attacks against an asset or person as well as cyberattacks. For example, details of a phishing strategy and the targets within the organization were discovered after being talked about in a darknet forum.
Monitor employee online activity. For example, this can allow security teams to identify employees who have been targeted and even blackmailed by cyber attackers for access to company data.
6 Ways Signal OSINT is Improving Protection for Executives and VIPs
Security teams need to be able to spot threats to executives and implement an effective response in a timely fashion. In this article, we take a look at 6 key areas that Signal OSINT is used by customers today to advance protection measures for high profile executives.
High profile executives and VIPs are more likely to receive threats of violence, be at the centre of negative online noise, and to be the target for both cyber and physical attacks. This, when paired with their busy schedules (which often involve travel), makes staying ahead of potential threats a particular challenge for their security teams.
Attackers have a variety of reasons and goals for targeting executives and VIPs. It could be anything ranging from a reaction to company layoffs, to kidnapping for ransom. Whatever the reason though, security teams need to be able to spot the threats, understand the motives, and implement an effective response in a timely fashion.
In this article, we take a look at 6 key ways Signal OSINT is used today by customers to advance protection measures for high profile executives.
How Can Signal OSINT Improve your Executive Security?
Discover private information published online
There are several reasons that an individual might publish private information online. Often, it is in anger or as some form of revenge. The kind of information that has been found published online includes: names, email addresses and logins, physical address, details about an executives families, passport details, medical information, credit card and bank details, and SSN’s.
Having such information leaks opens up an executive to a wide range of potential threats. As a security professional, it is vital to know if and when there is a data breach so that the threat can be neutralized. The longer data is available online the more risk there is. For example, if card details are discovered online the bank can be contacted and the card cancelled.
Read: Detecting and Mitigating the Risks of Data Breaches
Identify direct threats
Sometimes threat actors are more direct in the way they threaten executives. This could, for example, be a direct threat of violence through an email, instant messaging service or public forum like social media. While the majority of such threats come from so-called “keyboard warriors” there are some which will require further attention and action.
For example, discussions might be uncovered on the dark web forum with details of a planned attack on an executive. With the prior knowledge of the attack action can be taken to reduce the associated risks.
One way to differentiate between someone that is simply venting their anger on a public forum and someone who genuinely might take action is to look for repetition of negative sentiment.
Emotional analysis
Emotional analysis gives data extra context which allows it to be better understood enabling a more effective and accurate response to the potential risks.
It also allows you to differentiate between when a negative comment is simply that, a negative comment, or when it needs more serious attention, for example, it’s evolving into a physical threat.
Read: When Does Negative Sentiment Become a Threat?
Misinformation is spreading about an executive
The spread of disinformation is problematic on a number of levels. For example, throughout COVID-19 misinformation has been spread regarding the virus, it’s root causes and best prevention practices. This has harmed efforts to curtail and control it. Another recent example is the role of misinformation in the 2016 US election.
There are numerous reasons that individuals and organizations spread misinformation, it could be part of a phishing campaign or an international political assault, for example. Whatever the reason the results are almost always harmful. When an individual spreads misinformation around a CEO or other executive there are real ramifications for brand and reputation which need to be managed.
To combat misinformation organizations need to be equipped with the right tools and understand both what they’re looking for, and the reasons for spreading misinformation.
Disruptive events are planned which could prove a threat to executives.
Events such as protests planned at or near an office or manufacturing location could present logistical problems and delays as well as potentially devolve into riots which would represent a physical threat. Having intelligence on the events and any salient information regarding individuals or groups looking to create trouble will allow you to take appropriate precautionary measures and prevent a threat from escalating.
Travel risks
All travel comes with some inherent risk. However, it is more pronounced for executives who are at increased risk due to the regularity of their travel and high profile.
Additionally, events like extreme weather or terrorist action may make a destination unsafe. As such, having an OSINT solution such as Signal offering an early warning of any particular dangers will enable you to plan alternative routes and otherwise avoid high risk scenarios.
Read: 4 Aspects of Effective Executive Travel Risk Management
Early warnings with real-time data
Using Signal you can create customized alerts filtered via specific keywords, phrases or even locations. We also have a built-in translation tool so that data can be searched across languages and automatically translated into your default language.
Additionally, you can run alerts through our emotional analysis tool to determine how much of a threat any particular alert is. Finally, get our optional Sapphire bolt-on and utilise our skilled data analysts to further refine your results.
This approach allows your leave your intelligence gathering on autopilot and not only effectively reduce costs but vastly increase the scope of your monitoring ability and the overall amount of hyper-relevant intelligence at your fingertips. All of this allows you to gather actionable intel in realtime.
What is OSINT and how is it used for corporate security?
Open Source Intelligence (OSINT) gives security teams the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
There are good reasons why the fictional characters like Varys (Game of Thrones) are so influential in their respective worlds. The more information you have the more you can tailor and optimise strategies for your preferred outcome. However, whereas Varys has to contend with political scheming, assassination attempts and dragons, the modern (and real) world has a much broader plethora of potential attack vectors, many of which were unimaginable just 20 years ago.
Thankfully for security professionals, the broadening net of threats exists in a symbiotic relationship with intelligence sources and security tools. What this means is that while, yes, there are now more threats to contend with, there are also more solutions and tools. For example, artificial intelligence (AI) enables Centaur approaches that far exceed human or machine only results.
In this article, we take a look at how Open Source Intelligence (OSINT) can be and is being used to arm security teams with the ability to gather and analyse vast quantities of data and then enact effective plans to mitigate damage and even prevent threats.
The centaur model combines machines with human insights to get optimum results.
What is OSINT?
OSINT, as the name suggests, is data gathered from all publicly (openly) available data sources. These data sources could be anything from government records or archives, online discussion forums, blogs, social media posts, or the comments on those posts.
OSINT allows you to collect data from all of those sources at once, and because of the sheer amount of information that is shared and discussed continuously on every fathomable topic, it is an incredibly powerful tool. There are billions of historical records and millions more being posted every day. You can use OSINT to identify physical threat made against your organization or executives, discover data breaches, uncover terrorist plots and even get breaking news as it is happening.
In many situations, expert data analysts with OSINT tools can identify malicious actors and discover relationships, information which can be used to enhance a privacy and security plan.
How Organizations use OSINT
The need for organizations to employ OSINT as part of their corporate security processes is becoming increasingly more evident. Interestingly though the use of OSINT has been neither formalised nor widely adopted. It often takes a particular scenario to unfold before they even consider it.
A common example is a data breach. According to the Ponemon Institute’s 2018 Cost of a Data Breach Study, the average amount of time for a company to detect a data breach was 197 days. More often than not, the organization was not the first to know either. Utilising OSINT allows you to learn of data breaches as soon as discussions begin online, for example, the hacker offers up your data for sale.
This is just one way in which OSINT is used by businesses. The use of intelligence is immensely versatile. You can detect physical threats to assets or staff, determine travel risks, discover brand hazards, secure your social media channels and cybersecurity and more.
Despite the versatility of applications for OSINT tools it still often takes a worst-case scenario for an organization to decide to finally employ OSINT solutions.
Applications of OSINT as Cyber Intelligence
Most people freely share a large amount of data about themselves. In fact, in this day and age, it’s hard not to share your data. For example, almost everyone has a phone number, this phone number is likely connected with your name, address, date of birth, and email address. It might even be linked with your broadband connection and subsequently your IP address.
As an example, in 2019 T-mobile had a significant data breach. Thankfully, it appears they spotted and responded quickly, but not before some 1 million records were exposed. They were able to mitigate the damage but not prevent it. Other companies have historically been less quick to respond such as TerraCom and YourTel America who had to pay out $3.5 million USD collectively in damages in 2015 after their data breaches. Organizations also need to remember how everyday activities expose other forms of data such as shopping habits through credit card usage and location through fitness apps.
Intelligence isn’t just important for detecting breaches or hacks. It is also vital if organizations want to protect their staff from physical threats or from being exploited via phishing scams. For example, a company’s employees will likely all have social media accounts such as a LinkedIn account which details their roles and responsibilities. This information can be paired with information from other social profiles or information shared online and can, when used properly, become valuable intelligence on how an organization runs, who’s responsible for what, and even who a malicious actor should target.
Because of the various methods that security teams can use intelligence to protect a businesses interests having a dedicated team, armed with powerful OSINT tools like Signal, could save them from serious reputational and financial damages.
Examples of threats that Signal OSINT can detect and help protect against
Counterfeit or stolen property listed online - for example, counterfeit drugs.
Employee conduct, threats and harassment on social media.
Frustrated, angry or threatening customer correspondence.
Merger, acquisition & organizational partnership discussions - this could be important for ensuring smooth operation of the supply chain, for example.
Sensitive information publicly disclosed – accidentally or intentionally.
Presence of fake websites, fake invoices or scams targeting customers, staff or the organization - for example, a phishing website made to look like a banking institutes website and designed to encourage users to enter their password combination.
Credentials from data breach & compromised accounts belonging the organization.
Unsavoury relationships, membership or pending court action related to the organization.
The Results of Employing Powerful OSINT Tools
Experienced hackers and cybercriminals will understand the public nature of the channels and as such are likely to attempt to avoid actions that expose their intentions. However, OSINT doesn’t stop at the surface web, tools like Signal can give analysts and security teams access to data from sources such as the dark and deep web and even private dark web forums as well as more obscure surface websites.
The purpose of OSINT research is to provide teams with a thorough foundation of knowledge. Teams can subsequently use these insights to develop actionable plans to either prevent a threat from fully emerging, or minimise the damages of a current or recent attack.
One of the key issues that security teams and analysts face is the sheer amount of noise which might surround their brand. Invariably much of this noise is irrelevant to their purposes, however, some of it will be bad. This is why Signal assists with advanced filters applying boolean logic as well as features such as our emotional analysis tool.